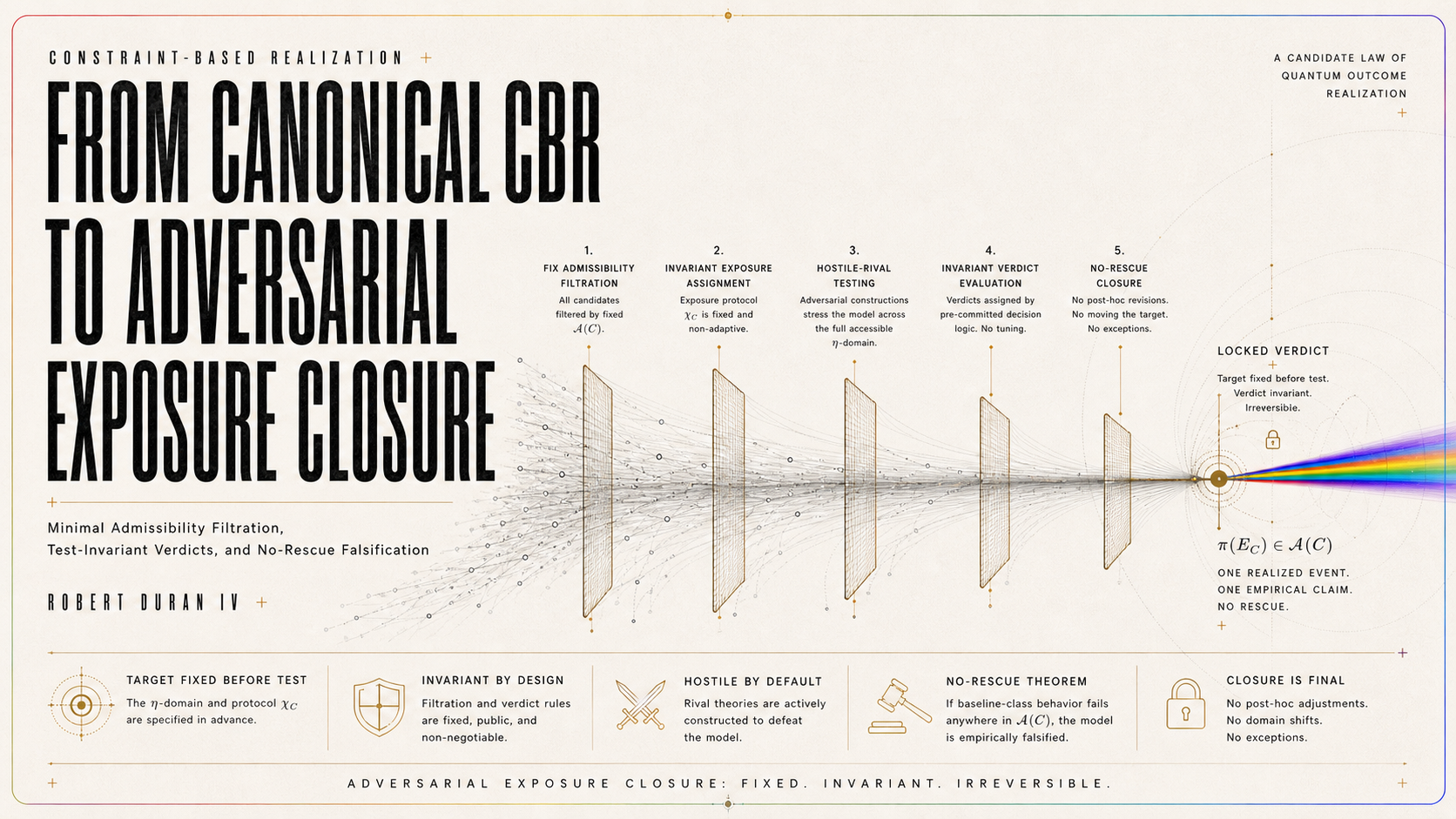
From Canonical Constraint-Based Realization (CBR) to Adversarial Exposure Closure
Abstract
Constraint-Based Realization, or CBR, has already been stated in canonical form as a candidate law of quantum outcome realization: a physically specified context C, a restricted admissible class 𝒜(C), a realization-burden functional ℛ_C(Φ) = αΞ_C(Φ) + βΩ_C(Φ) + γΛ_C(Φ), and a selected realization channel Φ*_C = argmin{ℛ_C(Φ) : Φ ∈ 𝒜(C)}. The canonical closure paper further establishes restricted uniqueness up to operational equivalence, local quadratic-weighting closure within canonical admissibility, an operational accessibility parameter η, a critical accessibility regime η_c, nuisance separation, detectability conditions, and a strong-null failure criterion. It presents CBR not as experimentally confirmed physics, but as a canonically specified and empirically vulnerable theory candidate.
This paper supplies the adversarial closure standard for empirical CBR. Its central claim is that CBR reaches full empirical seriousness only when every empirical claim is generated by a fixed admissibility filtration, classified by an invariant exposure map, tested against hostile rival models, and protected from post-failure rescue. The admissible class is made constructive by the filtration 𝒜(C) = F₆(C) / ≈_op. The burden functional is strengthened as the forced representation of admissibility within the stated theorem class. The empirical target relation is typed by π(E_C) ∈ 𝒜(C), while verdicts are assigned by χ_C : Emp_adm(C) / ≈_op → {supportive, falsifying, inadmissible}. Operationally equivalent test descriptions must receive the same verdict, η_c must be derived, bounded, or pre-registered before data, and a residual cannot count as CBR-supportive if hostile non-CBR rivals absorb it within τ.
The paper’s final closure rule is the No-Rescue Theorem: if an empirically admissible instantiation E_C fails under its own strong-null condition, then post-failure modification of η_c, γ, L_CBR, B, N, M_rival, S, κ, τ, or χ_C defines a new instantiation E′_C rather than rescuing E_C. The result is a complete adversarial exposure standard: CBR cannot move the target, absorb anomalies, depend on description choices, or revise away failure after the fact. A valid empirical CBR test must classify its result as supportive, falsifying, or inadmissible under fixed rules before interpretation begins.
1. Introduction: Why Canonical CBR Now Requires Adversarial Closure
The canonical CBR paper compresses the program into a theorem-bearing realization-law object. It distinguishes evolution, registration, and realization; defines the admissible class 𝒜(C); gives the law form Φ*_C = argmin{ℛ_C(Φ) : Φ ∈ 𝒜(C)}; establishes restricted uniqueness up to operational equivalence; gives a local probability-closure result; introduces η and η_c; and states a finite empirical burden under a designated accessibility-sensitive protocol family.
That canonical work answers the first seriousness question: Can CBR be stated as a mathematically constrained and empirically vulnerable realization-law candidate?
The answer supplied by the canonical paper is yes, within its declared scope.
But once that threshold is crossed, a harder burden appears. A theory with a canonical law form can still remain empirically underprotected if its admissible class is vague, its critical regime is movable, its signature is flexible, its nuisance class is expandable, its rivals are unspecified, or its failed instantiations can be revised after the fact and treated as continuous with the original claim.
The present paper therefore answers the adversarial closure question: Can CBR be tested in a way that prevents target movement, anomaly absorption, description-dependent verdicts, weak falsification, and post-failure rescue?
This is the next required step. A canonical theory candidate must not only state what it predicts. It must also state how empirical claims are admitted, how verdicts are assigned, how equivalent descriptions are kept verdict-equivalent, how rival explanations are defeated, and how failure remains failure once the test has been fixed.
Adversarial closure is the condition under which CBR can no longer protect itself by changing the test after the result is known. It is also the condition under which CBR cannot be unfairly dismissed by a weak or inadmissible test.
This paper forbids five moves:
No admissible class without a fixed filtration.
No empirical verdict without an invariant exposure map.
No CBR support without defeating hostile rivals.
No CBR falsification without strong-null satisfaction.
No rescue of a failed instantiation by post-data revision.
Adversarial closure does not make CBR true.
It makes CBR maximally testable.
It turns empirical CBR from a theory with a possible signature into a theory with fixed rules for support, falsification, inadmissibility, and revision.
2. Central Thesis
The central thesis of this paper is that canonical CBR becomes empirically complete only when its empirical claims are governed by an adversarial closure structure.
Canonical CBR supplies the realization-selection rule:
Φ*_C = argmin{ℛ_C(Φ) : Φ ∈ 𝒜(C)}
Adversarial exposure closure supplies the empirical-verdict rule:
χ_C : Emp_adm(C) / ≈_op → {supportive, falsifying, inadmissible}
These two maps play parallel roles. The first selects the realization channel from the canonically admissible class. The second classifies the empirical test from the empirically admissible exposure class.
The purpose of this paper is to force the second map to be as disciplined as the first.
A CBR empirical claim is adversarially closed only if four requirements are met.
First, the admissible class must be generated by a fixed filtration:
𝒜(C) = F₆(C) / ≈_op
The admissible class cannot be chosen after the result is known.
Second, the empirical instantiation must target a canonically admissible object:
π(E_C) ∈ 𝒜(C)
A test that does not project to a channel in the canonical admissible class is not a CBR test.
Third, the verdict must be assigned by an invariant exposure map:
χ_C : Emp_adm(C) / ≈_op → {supportive, falsifying, inadmissible}
The same operational test must receive the same verdict under equivalent descriptions.
Fourth, failure must be protected by a no-rescue rule. Once an empirically admissible instantiation E_C fails under its own strong-null condition, it cannot be rescued by changing η_c, γ, L_CBR, B, N, Δ_N, M_rival, S, κ, τ, or χ_C after the fact. Any such change defines a new instantiation:
E′_C ≠ E_C
The thesis can therefore be stated in one sentence:
CBR reaches adversarial closure only when every empirical claim is generated by a fixed admissibility filtration, classified by an invariant exposure map, tested against hostile rival models, and protected from post-failure rescue by a no-rescue rule.
This is not a restriction added from outside the theory. It is the empirical counterpart of CBR’s own canonical discipline. Just as realization selection must not depend on arbitrary representation, empirical verdicts must not depend on arbitrary test description, post-hoc parameter motion, or selective rival omission.
Adversarial closure is therefore the condition under which CBR becomes empirically decidable without becoming empirically plastic.
3. Typed Objects: Channels, Tests, Projections, and Verdicts
A precise CBR test requires a precise distinction between formal objects and empirical objects.
The canonical admissible class 𝒜(C) contains realization-compatible channels, or operational equivalence classes of such channels. Its elements are formal candidates for realization selection.
An empirical instantiation E_C is a different kind of object. It is not a channel. It is a complete test structure: physical apparatus, accessibility calibration, critical-regime declaration, predicted signature, baseline class, nuisance envelope, rival library, observable, dataset, scoring rule, thresholds, and verdict rule.
Therefore, the relation between an empirical test and the canonical theory cannot be written as:
E_C ∈ 𝒜(C)
That expression commits a type error.
The correct relation is a projection:
π(E_C) ∈ 𝒜(C)
where π(E_C) is the formal realization channel, or channel-family, that the empirical instantiation claims to test.
This projection is necessary but not sufficient.
A test may project to a canonically admissible target and still fail as an empirical test if it lacks calibration, parameter fixity, nuisance separation, rival resistance, sensitivity, or test-invariance.
Define:
Emp(C) = the class of proposed empirical CBR instantiations in context C.
Emp_adm(C) = the subclass of proposed empirical instantiations that satisfy adversarial admissibility.
Then:
Emp_adm(C) ⊂ Emp(C)
and:
E_C ∈ Emp_adm(C) only if π(E_C) ∈ 𝒜(C)
But:
π(E_C) ∈ 𝒜(C) does not imply E_C ∈ Emp_adm(C)
This is the first typing rule of adversarial exposure.
The second typing rule concerns descriptions. A test description is not yet the exposure object. Two descriptions may differ in notation, parameterization, model basis, or presentation while having the same operational content. Therefore empirical verdicts must be assigned not to arbitrary descriptions, but to operational equivalence classes.
Define:
ρ(E_C) = [E_C]_op
where [E_C]_op is the operational equivalence class of E_C under ≈_op.
The exposure map must therefore act on equivalence classes:
χ_C : Emp_adm(C) / ≈_op → {supportive, falsifying, inadmissible}
not on arbitrary descriptions.
This prevents description-dependent verdicts. If E_C and E′_C are operationally equivalent, then:
E_C ≈_op E′_C ⇒ χ_C(E_C) = χ_C(E′_C)
The third typing rule concerns failure. A failed empirical instantiation remains the same object only while its fixed commitments remain unchanged. If η_c, γ, L_CBR, B, N, Δ_N, M_rival, S, κ, τ, or χ_C are changed after failure, the result is not a rescue of E_C. It is a new object:
E′_C
Thus the typed structure is:
formal target: π(E_C) ∈ 𝒜(C)
empirical test: E_C ∈ Emp(C)
admissible empirical test: E_C ∈ Emp_adm(C)
operational exposure object: ρ(E_C) = [E_C]_op
verdict map: χ_C([E_C]_op) ∈ {supportive, falsifying, inadmissible}
post-failure modification: E′_C ≠ E_C
This structure makes the empirical side of CBR as disciplined as the formal side.
It prevents five confusions:
It prevents confusing a test with a channel.
It prevents confusing a formal target with an admissible empirical test.
It prevents confusing a description with an operational exposure object.
It prevents confusing a post-failure revision with a rescue.
It prevents confusing an anomaly with support.
That is why the typed framework is not cosmetic. It is the foundation of adversarial exposure closure.
4. Constructing 𝒜(C): The Admissibility Filtration
The canonical law form of CBR depends on the admissible class 𝒜(C). If 𝒜(C) is vague, adjustable, or selected after the fact, then the minimization rule
Φ*_C = argmin{ℛ_C(Φ) : Φ ∈ 𝒜(C)}
does not yet define a fully exposed theory. It defines only a formal selection rule whose domain remains under-specified. The present section closes that gap by giving a constructive procedure for 𝒜(C).
The central claim is that 𝒜(C) is not a free set of convenient candidates. It is the result of an ordered exclusion process. Beginning from a broad preliminary channel space Ch(C), the admissible class is obtained by removing candidates that violate the minimum conditions for a non-arbitrary realization law. The surviving candidates are then quotient by operational equivalence.
The construction is:
Ch(C) → F₁(C) → F₂(C) → F₃(C) → F₄(C) → F₅(C) → F₆(C) → 𝒜(C)
with:
𝒜(C) = F₆(C) / ≈_op
This filtration turns 𝒜(C) from a named admissible class into an auditable object.
A reviewer should be able to ask of any candidate channel:
Where does it enter?
Which filtration stages does it survive?
Which stage excludes it, if any?
What operational equivalence class remains after quotienting?
If those questions cannot be answered, then 𝒜(C) has not been specified strongly enough for adversarial exposure.
4.1 Context Specification
Before the filtration begins, the measurement context C must be physically specified.
C is not merely a choice of observable, basis, or outcome label. It is the complete realization-relevant physical context. At minimum, C must specify:
the system degrees of freedom,
the apparatus degrees of freedom,
the state or Hilbert-space description used for the context,
the interaction architecture,
the record-bearing degrees of freedom,
the environmental couplings relevant to registration,
the timing relations relevant to record formation and retrieval,
the accessibility channels,
the operational readout procedures,
and the protocol family in which the test is embedded.
This requirement is not decorative. CBR treats realization as context-indexed. Therefore the context must contain enough physical structure to determine what counts as an admissible realization-compatible channel. If C is under-specified, then 𝒜(C) is under-specified. If 𝒜(C) is under-specified, then Φ*_C is not yet a determinate realization verdict.
Thus the first adversarial demand is:
No physically specified C, no admissible 𝒜(C).
4.2 Preliminary Candidate Space Ch(C)
Let Ch(C) denote the preliminary class of formally writable candidate realization channels associated with context C.
Ch(C) is intentionally broad. It includes channels that may later be excluded. Its purpose is not to define admissibility, but to provide the starting domain on which the filtration acts.
A member Φ ∈ Ch(C) is a candidate only in the preliminary sense. It is not yet a CBR-admissible realization channel. It becomes CBR-admissible only if it survives every exclusion stage and is then considered modulo operational equivalence.
This distinction matters because it prevents the admissible class from being constructed by intuition. The procedure begins with broad formal availability and then removes candidates for explicit reasons.
The filtration therefore has the following form:
F₀(C) = Ch(C)
and each later stage satisfies:
F₆(C) ⊆ F₅(C) ⊆ F₄(C) ⊆ F₃(C) ⊆ F₂(C) ⊆ F₁(C) ⊆ F₀(C)
Only after all exclusions are complete do we define:
𝒜(C) = F₆(C) / ≈_op
4.3 F₁: Dynamical Compatibility
Define:
F₁(C) = {Φ ∈ Ch(C) : Φ is dynamically compatible with the ordinary quantum dynamics outside realization selection}
This stage excludes dynamical leakage.
CBR is not introduced as a replacement for ordinary quantum evolution. The canonical paper explicitly distinguishes evolution, registration, and realization, with CBR located at the realization layer rather than as a wholesale substitute for quantum dynamics.
A candidate channel fails F₁ if it covertly changes the baseline dynamics and then attributes the resulting difference to realization. Such a channel does not test CBR as a realization law. It tests an undeclared dynamical modification.
Examples of F₁ failure include:
a channel that changes ordinary unitary or open-system propagation outside the declared realization layer,
a channel that alters baseline decoherence behavior without declaring this as a new dynamical postulate,
a channel that produces the desired outcome by rewriting the underlying state evolution,
or a channel whose empirical signature is actually caused by non-CBR dynamics smuggled into the realization map.
The adversarial rule is:
CBR may add a realization-selection law, but it may not hide an ordinary-dynamics revision inside that law.
If Φ fails this rule, then:
Φ ∉ F₁(C)
4.4 F₂: Representational Invariance
Define:
F₂(C) = {Φ ∈ F₁(C) : Φ is invariant under physically irrelevant reformulations of C}
This stage excludes representational dependence.
A realization law that changes verdict under notation is not a physical law of realization. If two descriptions of the same context differ only by relabeling, equivalent encoding, coordinate convention, basis notation, or operationally null reformulation, then an admissible realization channel must treat them equivalently.
A candidate channel fails F₂ if its verdict depends on:
outcome labels,
branch names,
basis notation without operational difference,
coordinate parameterization,
choice of equivalent encoding,
or decomposition conventions that do not alter the physical context.
This stage corresponds to the burden term Ξ_C. The canonical burden functional includes Ξ_C precisely because representational non-invariance is a law-level defect.
The adversarial rule is:
No realization verdict may depend on a physically irrelevant description choice.
If Φ fails this rule, then:
Φ ∉ F₂(C)
4.5 F₃: Record-Structural Coherence
Define:
F₃(C) = {Φ ∈ F₂(C) : Φ is coherent with physically relevant record structure}
This stage excludes record incoherence.
CBR distinguishes realization from both ordinary evolution and mere registration. But realization cannot float free from record structure. If outcome-defining records are physically relevant to the measurement context, then a realization channel must respect that record-bearing structure. It cannot select based on arbitrary formal decompositions that have no record-level significance.
A candidate channel fails F₃ if it selects based on:
purely formal branch labels,
unsupported fine-grainings,
non-record-bearing distinctions,
mathematical decompositions with no operational record consequence,
or abstract alternatives that do not correspond to physically relevant registration structure.
This stage corresponds to the burden term Ω_C. Ω_C penalizes record-structural incoherence, thereby preventing CBR from becoming a branch-labeling exercise disconnected from physical measurement records.
The adversarial rule is:
A realization channel must track physically relevant record structure, not formal surplus.
If Φ fails this rule, then:
Φ ∉ F₃(C)
4.6 F₄: Accessibility Consistency
Define:
F₄(C) = {Φ ∈ F₃(C) : Φ treats accessibility-equivalent structures equivalently and accessibility-distinct structures according to the declared accessibility burden}
This stage excludes accessibility arbitrariness.
The canonical paper introduces η as an operational accessibility parameter and η_c as the critical accessibility regime in which accessibility may become realization-effective. It places empirical CBR under a designated accessibility-sensitive protocol family and a finite failure condition.
Therefore accessibility cannot remain a loose word. It must enter the admissibility structure operationally.
A candidate channel fails F₄ if it:
treats accessibility-equivalent situations differently,
treats accessibility-distinct situations as equivalent when accessibility is declared realization-relevant,
responds to apparatus labels rather than operational accessibility,
allows η to be fitted from the same residuals used to claim CBR support,
or introduces accessibility dependence without a declared Λ_C relation.
This stage corresponds to the burden term Λ_C. Λ_C penalizes accessibility inconsistency and provides the formal route by which accessibility becomes law-relevant rather than merely interpretive.
The adversarial rule is:
Accessibility may enter CBR only through operationally calibrated, equivalence-respecting structure.
If Φ fails this rule, then:
Φ ∉ F₄(C)
4.7 F₅: Probabilistic Non-Insertion
Define:
F₅(C) = {Φ ∈ F₄(C) : Φ does not covertly insert the target probability rule}
This stage excludes probability insertion.
CBR must not obtain its probability structure by hiding the desired result in its starting assumptions. The canonical paper explicitly treats local quadratic-weighting closure as a result within canonical admissibility, not as a universal assumption imported without burden.
A candidate channel fails F₅ if it:
assumes Born weighting inside the admissibility definition,
uses a metric that already privileges quadratic weighting without independent justification,
builds the target weighting into the refinement class,
normalizes in a way that smuggles in the desired rule,
or uses probability-matching as an independent burden term before deriving or justifying it.
The adversarial rule is:
A probability rule cannot be counted as derived if it was already inserted into admissibility.
If Φ fails this rule, then:
Φ ∉ F₅(C)
4.8 F₆: Empirical Exposure Eligibility
Define:
F₆(C) = {Φ ∈ F₅(C) : Φ has a declared exposure route if the instantiation claims empirical status}
This stage excludes empirical idleness.
A purely formal channel may be discussed as a mathematical object. But an empirical CBR instantiation must not be indefinitely shielded from possible support or failure. If the instantiation claims empirical standing, then it must identify how the channel enters an exposure map.
A candidate channel fails F₆ if it:
has no declared observable consequence in the proposed empirical setting,
cannot be tied to η, η_c, or another declared operational control variable,
cannot be placed under a nuisance-separated comparison,
cannot be tested against a baseline class,
or lacks a public condition under which the instantiation fails.
This stage corresponds to the empirical exposure axiom in the canonical architecture. The canonical paper presents CBR as finitely exposed through a designated protocol family and a strong-null failure criterion.
The adversarial rule is:
An empirical CBR instantiation must expose its tested channel to a public verdict condition.
If Φ fails this rule, then:
Φ ∉ F₆(C)
4.9 Operational Equivalence Quotient
After the filtration stages are complete, the surviving candidates must be quotient by operational equivalence.
Define:
Φ ≈_op Ψ
when no admissible observation, record relation, accessibility relation, or realization-relevant operational consequence distinguishes Φ from Ψ in context C.
The admissible class is then:
𝒜(C) = F₆(C) / ≈_op
This quotient is essential. CBR should not count syntactic differences as physically distinct realization channels. If two surviving channels differ only by operationally null reformulation, they belong to the same admissible verdict class.
This mirrors the canonical paper’s restricted uniqueness claim: realization is not required to be unique at the level of every syntactic representative, but unique up to operational equivalence.
The adversarial rule is:
The admissible class contains operational channel classes, not arbitrary descriptions.
4.10 Section Result
This section establishes the constructive form of 𝒜(C):
𝒜(C) = F₆(C) / ≈_op
where F₆(C) is obtained by excluding:
dynamically incompatible channels,
representation-dependent channels,
record-incoherent channels,
accessibility-incoherent channels,
probability-inserting channels,
and empirically idle channels.
The construction makes 𝒜(C) auditable. It prevents the admissible class from being chosen after the fact. It also prepares the next theorem: if any filtration stage is removed, a distinct hostile-review failure mode re-enters the framework.
5. Minimal Filtration Theorem
The previous section defined 𝒜(C) constructively. The present section proves that the filtration is not merely useful but necessary. Each filtration stage blocks a distinct form of arbitrariness. Removing any stage reopens a hostile-review objection that adversarial CBR must close.
The theorem does not claim that the filtration is the only conceivable way to describe admissibility in every possible formal language. It claims something narrower and stronger: within the adversarial exposure standard for canonical CBR, the filtration stages F₁ through F₆ are minimally necessary because each removes a distinct failure mode not removed by the others.
5.1 The Six Failure Modes
The filtration blocks six hostile-review failure modes.
F₁ blocks dynamical leakage.
F₂ blocks representational dependence.
F₃ blocks record incoherence.
F₄ blocks accessibility arbitrariness.
F₅ blocks probability insertion.
F₆ blocks empirical idleness.
These are independent failure modes. A channel may be dynamically compatible but representation-dependent. It may be representation-invariant but record-incoherent. It may respect record structure but treat accessibility arbitrarily. It may handle accessibility but smuggle in probability. It may avoid probability insertion but remain empirically idle.
Therefore no stage is redundant.
5.2 Theorem 1: Minimal Filtration Theorem
Let C be a physically specified measurement context and Ch(C) the preliminary candidate channel space. Let 𝒜(C) be constructed by the filtration:
Ch(C) → F₁(C) → F₂(C) → F₃(C) → F₄(C) → F₅(C) → F₆(C) → 𝒜(C)
with:
𝒜(C) = F₆(C) / ≈_op
Then, for an empirical CBR test to be non-arbitrary under adversarial exposure closure, each filtration stage F₁ through F₆ is necessary. If any stage is removed, the resulting construction permits at least one hostile-review failure mode: dynamical leakage, representational dependence, record incoherence, accessibility arbitrariness, probability insertion, or empirical idleness.
5.3 Proof
Assume first that F₁ is removed. Then a candidate channel may survive even if it covertly modifies ordinary quantum dynamics outside the declared realization layer. In that case, an observed deviation may be caused by an undeclared dynamical change rather than by CBR realization selection. The empirical test no longer isolates CBR as a realization law. Therefore F₁ is necessary.
Assume next that F₂ is removed. Then a candidate channel may survive even if its verdict changes under relabeling, equivalent encoding, basis notation, or coordinate convention. The theory would then respond to description rather than physical content. Since a physical realization law must be invariant under irrelevant reformulation, F₂ is necessary.
Assume next that F₃ is removed. Then a candidate channel may survive even if it selects based on formal branch distinctions or fine-grainings with no record-bearing significance. Such a channel would confuse mathematical decomposition with physical measurement structure. Since CBR is a theory of outcome realization in record-bearing contexts, F₃ is necessary.
Assume next that F₄ is removed. Then a candidate channel may survive even if it treats accessibility-equivalent contexts differently, ignores declared accessibility relevance, or responds to accessibility without operational calibration. The resulting empirical signature could depend on arbitrary implementation labels rather than the accessibility burden Λ_C. Since canonical CBR makes accessibility central to its empirical exposure, F₄ is necessary.
Assume next that F₅ is removed. Then a candidate channel may survive even if it inserts the target probability rule into the admissibility structure. The local probability-closure result would then be vulnerable to circularity: the theory could appear to derive the weighting it had already assumed. Since CBR requires probabilistic non-insertion, F₅ is necessary.
Assume finally that F₆ is removed. Then a candidate channel may survive in an empirical instantiation even though it has no declared exposure route, no observable burden, no nuisance-separated comparison, and no failure condition. Such a channel could be discussed formally, but it could not support an empirical CBR claim. Since adversarial closure concerns empirical exposure, F₆ is necessary.
Each filtration stage therefore blocks a distinct defect. Removing any one stage reopens a corresponding arbitrariness mode. Hence all six stages are minimally necessary for adversarial empirical closure.
5.4 Corollary 1: No Filtration Trace, No Admissible Class
If a proposed empirical CBR test cannot provide the filtration trace from Ch(C) to 𝒜(C), then 𝒜(C) is not sufficiently specified for adversarial exposure.
The required trace is:
Ch(C) → F₁(C) → F₂(C) → F₃(C) → F₄(C) → F₅(C) → F₆(C) → 𝒜(C)
A paper may still discuss a proposed class informally. But it cannot claim adversarially closed empirical status without showing how the class is constructed.
5.5 Corollary 2: 𝒜(C) Is Not Adjustable After Data
Because every filtration stage removes a distinct failure mode, 𝒜(C) cannot be expanded, narrowed, or reinterpreted after the empirical outcome is known.
If the admissible class is changed after data inspection, the original empirical instantiation E_C is no longer being tested. A new instantiation E′_C has been created.
Thus:
post-data modification of 𝒜(C) ⇒ E′_C ≠ E_C
This is an admissible revision only if it is treated as a new proposal requiring a new exposure map.
5.6 Corollary 3: The Filtration Is the First Anti-Rescue Device
The no-rescue rule begins at the level of 𝒜(C). If a failed empirical instantiation is repaired by adding or removing candidates from the admissible class after the fact, the repair does not rescue the failed test. It defines a new test.
The original E_C remains failed, inadmissible, or unsupported according to its original filtration.
5.7 Section Result
This section proves that the admissibility filtration is not optional scaffolding. It is the minimal exclusion sequence needed to produce a non-arbitrary empirical CBR test. Each filtration stage blocks a distinct hostile-review failure mode, and no stage can be removed without reopening that failure mode.
The next section shows that once this filtration is fixed, the canonical burden functional ℛ_C is not merely convenient. It is the forced burden representation of the surviving admissibility structure within the stated theorem class.
6. Burden Representation Theorem
The admissibility filtration constructs 𝒜(C). The next question is whether the burden functional ℛ_C is merely chosen or structurally forced.
The canonical burden functional is:
ℛ_C(Φ) = αΞ_C(Φ) + βΩ_C(Φ) + γΛ_C(Φ)
The canonical paper presents Ξ_C, Ω_C, and Λ_C as the burden terms corresponding to representational invariance, record-structural coherence, and accessibility consistency.
The present section strengthens that claim. Within the adversarial exposure theorem class, any realization law that survives the admissibility filtration and satisfies the required invariance, record, accessibility, probability, and exposure constraints is representable by a burden functional equivalent to αΞ_C + βΩ_C + γΛ_C, up to positive rescaling and operationally null terms.
This does not claim universal metaphysical inevitability across every conceivable realization theory. It claims conditional structural necessity within canonical CBR’s admissibility class.
6.1 Admissibility Preorder
Once the filtration is fixed, the surviving candidate channel classes are not merely admitted or excluded. They also carry degrees of burden.
Some surviving candidates may better satisfy representational invariance, record-structural coherence, and accessibility consistency than others. Therefore the filtration induces an admissibility preorder on operational channel classes.
Write:
[Φ] ≤_C [Ψ]
to mean that [Φ] carries no greater admissibility burden than [Ψ] in context C.
This preorder is defined on:
𝒜(C) = F₆(C) / ≈_op
The burden functional ℛ_C is a scalar representation of that preorder.
6.2 Burden Equivalence
Two burden functionals ℛ_C and ℛ′_C are burden-equivalent, written:
ℛ_C ≡_B ℛ′_C
if they induce the same ordering of admissible operational channel classes in 𝒜(C), up to:
positive rescaling,
positive affine transformation,
and operationally null terms.
This definition matters because the exact numerical representation of a burden is not physically primary. What matters is the admissibility ordering it induces over operational channel classes.
Thus the claim is not that one specific notation for ℛ_C is sacred. The claim is that any admissibility-respecting representation must be equivalent to the canonical burden structure.
6.3 Burden Coordinates
The filtration identifies three surviving burden coordinates.
First, F₂ forces a representational burden. Any realization law must penalize dependence on physically irrelevant reformulation. This burden is Ξ_C.
Second, F₃ forces a record-structural burden. Any realization law must penalize selection that fails to track physically relevant record-bearing structure. This burden is Ω_C.
Third, F₄ forces an accessibility burden. Any realization law that makes accessibility realization-relevant must penalize incoherent treatment of operational accessibility. This burden is Λ_C.
F₁ is a boundary condition: it prevents the realization law from becoming an undeclared dynamics revision.
F₅ is a prohibition: it prevents the target probability rule from being inserted as a separate burden.
F₆ is an exposure condition: it prevents empirically idle additions in empirical instantiations.
Therefore the surviving positive burden coordinates are exactly:
Ξ_C, Ω_C, Λ_C
This is why the canonical functional has the form:
ℛ_C = αΞ_C + βΩ_C + γΛ_C
6.4 Theorem 2: Burden Representation Theorem
Let L be any realization law on context C satisfying the adversarial CBR admissibility conditions:
dynamical compatibility,
representational invariance,
record-structural coherence,
accessibility consistency,
probabilistic non-insertion,
operational equivalence,
and empirical exposure.
Suppose the admissibility filtration is nonempty and the induced admissibility preorder on 𝒜(C) is regular, separable, and stable under coarse-graining, refinement, and composition.
Then L is representable by a burden functional burden-equivalent to:
ℛ_C(Φ) = αΞ_C(Φ) + βΩ_C(Φ) + γΛ_C(Φ)
up to positive rescaling and operationally null terms.
6.5 Proof
Because F₁ has been imposed, the law cannot use ordinary dynamical modification as a hidden burden coordinate. Any candidate that does so has already been excluded. Thus the burden representation is confined to realization-selection structure.
Because F₂ has been imposed, the law must distinguish candidates that differ in representational invariance. A burden coordinate is therefore required to penalize dependence on physically irrelevant reformulation. This coordinate is Ξ_C.
Because F₃ has been imposed, the law must distinguish candidates that differ in record-structural coherence. A burden coordinate is therefore required to penalize failure to track physically relevant record-bearing structure. This coordinate is Ω_C.
Because F₄ has been imposed, the law must distinguish candidates that differ in accessibility consistency. A burden coordinate is therefore required to penalize incoherent treatment of operational accessibility. This coordinate is Λ_C.
Because F₅ has been imposed, no independent probability-matching burden may be added unless it is derived separately rather than inserted. Therefore a direct Born-matching term is excluded from the canonical burden representation.
Because F₆ has been imposed, empirically idle terms are excluded from empirical instantiations. A burden coordinate that has no operational consequence or exposure route cannot enter the adversarial empirical representation.
The remaining admissibility differences are therefore exhausted by representational, record-structural, and accessibility burdens. Under regularity and separability, the admissibility preorder admits scalar representation. Under stability across coarse-graining, refinement, and composition, the representation must preserve the same ordering across equivalent admissibility transformations.
Therefore the law is representable by:
ℛ_C(Φ) = αΞ_C(Φ) + βΩ_C(Φ) + γΛ_C(Φ)
up to positive rescaling and operationally null terms.
6.6 Corollary 4: ℛ_C Is Not a Fit Function
The coefficients α, β, and γ are theory-level burden parameters. They cannot be adjusted after outcome inspection to rescue CBR from a null result or to amplify an observed anomaly.
If α, β, or γ are moved after data, then the original empirical instantiation E_C is no longer being tested. A new empirical instantiation E′_C has been created.
Thus:
post-data movement of α, β, or γ ⇒ E′_C ≠ E_C
6.7 Corollary 5: No Independent Probability Term Without Derivation
A burden term that directly rewards agreement with the desired probability rule is inadmissible unless independently derived from the canonical admissibility structure.
Otherwise the probability result is circular.
Therefore the canonical burden cannot be supplemented by an undeclared probability-matching term such as:
+ λP_C(Φ)
where P_C simply penalizes deviation from the target weighting rule.
Such a term would violate probabilistic non-insertion unless P_C is separately justified by a theorem independent of the desired conclusion.
6.8 Corollary 6: No Empirically Idle Burden Term
A burden term with no empirical exposure route cannot enter an empirical CBR instantiation claiming adversarial closure.
If a proposed term has no effect on admissible verdicts, no relation to η or another operational control variable, no nuisance-separated observable consequence, and no failure condition, then it is operationally idle.
Operationally idle terms may be discussed as mathematical extensions, but they cannot support an empirical CBR claim.
6.9 Scope of the Theorem
The Burden Representation Theorem is conditional.
It does not claim that every logically possible realization law in every framework must reduce to CBR. It claims that within the adversarial CBR theorem class—where dynamical compatibility, representational invariance, record coherence, accessibility consistency, probabilistic non-insertion, operational equivalence, and empirical exposure are required—the canonical burden structure is forced up to burden equivalence.
This scope is important. The theorem is strong because it is exact about its domain.
It says:
Within this admissibility class, ℛ_C is not optional.
It does not say:
No other metaphysical framework can ever be imagined.
That restraint makes the result more credible.
6.10 Section Result
This section establishes that once 𝒜(C) is constructed by the minimal filtration, the canonical burden functional is not merely a preferred design. It is the burden representation forced by the surviving admissibility structure.
The result is:
ℛ_C(Φ) ≡_B αΞ_C(Φ) + βΩ_C(Φ) + γΛ_C(Φ)
within the stated theorem class.
This closes a major hostile-review objection. A critic can no longer say that ℛ_C is simply chosen because it is convenient, unless they reject one of the filtration stages or one of the theorem conditions. The debate is thereby sharpened: the critic must identify which admissibility burden is unnecessary, which filtration stage is invalid, or which representation assumption fails.
That is exactly the function of a publication-ready theorem standard.
7. Empirical Exposure Map χ_C
Canonical CBR supplies a realization-selection rule:
Φ*_C = argmin{ℛ_C(Φ) : Φ ∈ 𝒜(C)}
This rule determines the selected realization channel, up to operational equivalence, from the canonically admissible class. The canonical paper thereby fixes the formal object of CBR as a realization-law candidate rather than a merely interpretive description.
Adversarial empirical CBR requires a parallel object. If canonical CBR selects realization channels, empirical CBR must classify tests. The corresponding empirical object is the exposure-classification map:
χ_C : Emp_adm(C) / ≈_op → {supportive, falsifying, inadmissible}
This map is not optional. Without χ_C, an experiment may produce data, residuals, plots, and interpretations, but it does not expose CBR to a determinate empirical verdict. A valid empirical CBR test must be able to say, before outcome inspection, what result would count as support, what result would count as falsification, and what failure of test conditions would make the result inadmissible.
The exposure map is therefore the empirical counterpart of the canonical selection rule.
Canonical side:
Φ*_C = argmin{ℛ_C(Φ) : Φ ∈ 𝒜(C)}
Empirical side:
χ_C([E_C]_op) ∈ {supportive, falsifying, inadmissible}
The first map prevents arbitrary realization selection.
The second map prevents arbitrary empirical interpretation.
7.1 Definition: Empirical Instantiation
An empirical instantiation of CBR in context C is the structured object:
E_C = ⟨π, ρ, C, 𝒜(C), ℛ_C, Θ_CBR, η, g, η_c, I_c, L_CBR, B, N, Δ_N, M_rival, V, D, S, κ, τ⟩
where each component must be fixed or declared before confirmatory interpretation.
The components are as follows.
π is the projection from the empirical instantiation to the formal target under test:
π(E_C) ∈ 𝒜(C)
This prevents the empirical test from floating free of the canonical admissible class.
ρ maps the empirical test description to its operational equivalence class:
ρ(E_C) = [E_C]_op
This prevents the verdict from depending on notation, parameterization, or presentation.
C is the physically specified measurement context.
𝒜(C) is the admissible class constructed by the filtration:
𝒜(C) = F₆(C) / ≈_op
ℛ_C is the canonical realization-burden functional:
ℛ_C(Φ) = αΞ_C(Φ) + βΩ_C(Φ) + γΛ_C(Φ)
Θ_CBR is the set of theory and protocol parameters, including at minimum:
Θ_CBR = {α, β, γ, δ, ε, τ}
η is the operational accessibility parameter.
g is the accessibility-calibration map:
η = g(s)
where s denotes the directly controlled laboratory settings.
η_c is the critical accessibility value or bounded critical regime.
I_c is the predeclared critical interval around η_c.
L_CBR is the predicted CBR accessibility signature.
B is the declared standard quantum/decoherence baseline class.
N is the declared nuisance class.
Δ_N is the nuisance envelope.
M_rival is the hostile rival-model library.
V is the primary observable, such as visibility V(η).
D is the confirmatory dataset.
S is the predeclared model-scoring or decision functional.
κ is the required model-separation margin.
τ is the detection or resolution threshold.
This definition makes clear that an empirical CBR test is not just an apparatus. It is a full verdict-bearing structure.
7.2 Definition: Empirical Admissibility
An empirical instantiation E_C belongs to Emp_adm(C) only if all of the following conditions hold.
First, the formal target must be canonically admissible:
π(E_C) ∈ 𝒜(C)
Second, 𝒜(C) must have been constructed by the admissibility filtration, not chosen post-hoc.
Third, η must be independently calibrated.
Fourth, η_c or its critical interval must be derived, bounded, or pre-registered before confirmatory data inspection.
Fifth, δ, ε, τ, α, β, and γ must be fixed before data, or varied only within predeclared ranges.
Sixth, L_CBR must be restricted before data in location, width, sign, magnitude, morphology, and relation to Λ_C.
Seventh, B must be declared before data.
Eighth, N and Δ_N must be declared before data.
Ninth, M_rival must be declared before data.
Tenth, S and κ must be declared before data.
Eleventh, χ_C must be invariant under operationally equivalent descriptions.
Twelfth, the experiment must have sufficient sensitivity to detect ε inside the critical interval.
If any of these conditions fails, then:
E_C ∉ Emp_adm(C)
and the verdict is not supportive or falsifying. It is:
χ_C([E_C]_op) = inadmissible
This is the key adversarial rule: inadmissibility is not weak support and not weak falsification. It is failure to enter the exposure relation.
7.3 Definition: Exposure Classification
The exposure map assigns one of three verdicts.
Supportive
χ_C([E_C]_op) = supportive
only if E_C is empirically admissible, the predicted L_CBR appears in I_c, the feature matches the predeclared signature form, the residual exceeds Δ_N + τ, negative controls do not show the same feature, and the CBR model defeats all declared rivals by at least κ.
Falsifying
χ_C([E_C]_op) = falsifying
only if E_C is empirically admissible, the strong-null conditions are satisfied, the experiment had sufficient power to detect ε, and the predicted L_CBR does not appear in I_c beyond the declared tolerance.
Inadmissible
χ_C([E_C]_op) = inadmissible
if the test lacks empirical admissibility, lacks test-invariance, lacks independent η-calibration, lacks fixed η_c, lacks restricted L_CBR, lacks nuisance bounds, lacks rival declaration, lacks power, or permits post-data revision of verdict-relevant structure.
Thus χ_C is not a loose interpretive label. It is a verdict rule.
7.4 Exposure Map Theorem
Theorem 3: Empirical Exposure Map Theorem
Let E_C be a proposed empirical CBR instantiation in context C. A determinate empirical verdict for E_C exists only if there is a well-defined exposure map:
χ_C : Emp_adm(C) / ≈_op → {supportive, falsifying, inadmissible}
such that χ_C acts on operational equivalence classes [E_C]_op and not on arbitrary descriptions of E_C.
If χ_C is not defined before confirmatory interpretation, or if χ_C depends on arbitrary description choices, then E_C is empirically inadmissible.
7.5 Proof
A CBR empirical test can support the theory only if the support condition is fixed before the result is known. Otherwise any favorable anomaly can be redescribed as support.
A CBR empirical test can falsify the theory only if the failure condition is fixed before the result is known. Otherwise the theory can escape failure by altering the tested commitments.
A CBR empirical test can be judged inadmissible only if the admissibility requirements are fixed before the result is known. Otherwise weak or underdefined tests can be misused as support or falsification.
Therefore a valid empirical exposure requires a predeclared map from admissible operational test classes to verdicts. Since descriptions of the same test may differ without operational difference, χ_C must act on [E_C]_op rather than on arbitrary descriptions.
If no such χ_C exists, the experiment may be exploratory, but it is not a confirmatory CBR test.
7.6 Corollary: No χ_C, No Empirical Exposure
If a proposed CBR experiment cannot define χ_C before outcome inspection, then CBR is not empirically exposed by that experiment.
The result may still motivate later work, but it cannot validly support or falsify the tested CBR instantiation.
7.7 Section Result
This section establishes χ_C as the empirical counterpart of the canonical selection rule. The formal theory selects realization channels by minimizing ℛ_C over 𝒜(C). The empirical theory classifies tests by applying χ_C to operational equivalence classes of admissible empirical instantiations.
The result is:
canonical selection requires Φ*_C
empirical exposure requires χ_C
Without Φ*_C, CBR has no canonical realization verdict.
Without χ_C, CBR has no empirical verdict.
8. Operational Equivalence and Test-Invariant Verdicts
The canonical theory requires invariance under physically irrelevant reformulation. A realization law that changes verdict under relabeling, equivalent encoding, or notation is not physically selecting. It is responding to representation.
The same principle must govern empirical exposure. A CBR test cannot be supportive under one description and falsifying under an operationally equivalent description. If the physical content, accessibility structure, records, baseline, nuisance class, rival models, and decision rule are the same, then the verdict must be the same.
This section makes that requirement explicit.
Canonical CBR requires representation-invariant realization selection.
Adversarial empirical CBR requires representation-invariant verdict classification.
8.1 Definition: Operational Equivalence of Empirical Instantiations
Two empirical instantiations E_C and E′_C are operationally equivalent, written:
E_C ≈_op E′_C
if they have the same exposure-relevant operational content.
That means they agree on:
the physical context C,
the accessible records,
the η-calibration content,
the critical regime I_c,
the predicted signature L_CBR,
the baseline class B,
the nuisance class N,
the nuisance envelope Δ_N,
the rival library M_rival,
the primary observable V,
the decision rule S,
the separation margin κ,
the detection threshold τ,
the strong-null condition,
and the observable consequences.
They may differ in:
notation,
coordinate labels,
parameter names,
model basis,
equivalent encoding,
symbolic presentation,
or decomposition convention.
Operational equivalence is therefore not syntactic identity. It is sameness of verdict-relevant empirical content.
8.2 Definition: Operational Exposure Object
The exposure object is not the raw description E_C. It is the operational equivalence class:
ρ(E_C) = [E_C]_op
Thus χ_C should be written as:
χ_C([E_C]_op)
rather than as a verdict on a preferred description.
This is essential. A description may contain arbitrary choices. An operational equivalence class removes those arbitrary choices.
The empirical exposure object is therefore:
[E_C]_op ∈ Emp_adm(C) / ≈_op
not merely:
E_C ∈ Emp_adm(C)
8.3 Exposure Invariance Theorem
Theorem 4: Exposure Invariance Theorem
Let E_C and E′_C be operationally equivalent empirical instantiations of the same CBR test.
If χ_C is a valid empirical exposure map, then:
E_C ≈_op E′_C ⇒ χ_C(E_C) = χ_C(E′_C)
Equivalently:
χ_C(E_C) = χ_C([E_C]_op)
If two operationally equivalent descriptions yield different classifications, then χ_C is not well-defined and the test is empirically inadmissible.
8.4 Proof
Operationally equivalent empirical instantiations contain the same exposure-relevant physical content. They have the same accessible records, same η-calibration, same critical regime, same predicted signature, same baseline class, same nuisance structure, same rival library, same observable consequences, and same decision rule.
If χ_C assigns different verdicts to E_C and E′_C, the difference cannot arise from empirical content. It must arise from notation, labeling, parameterization, decomposition, or presentation.
A verdict that depends on such features is not an empirical verdict. It is a description-dependent artifact.
Therefore a valid χ_C must be invariant over operational equivalence classes.
8.5 Corollary: The Description-Dependence Loophole Is Closed
A CBR result cannot depend on a preferred description of the same experiment.
The following changes cannot alter the verdict if operational content is unchanged:
renaming η,
rescaling η by an allowed operationally equivalent transformation,
rewriting the same baseline in a different basis,
moving notation around without changing the nuisance envelope,
renaming rival-model parameters,
using equivalent model coordinates,
or presenting the same decision rule in different mathematical form.
If such a change alters the verdict, then the descriptions were not operationally equivalent or the exposure map was not valid.
8.6 Corollary: Test-Invariance Is the Empirical Analogue of Ξ_C
In the canonical burden functional:
ℛ_C = αΞ_C + βΩ_C + γΛ_C
Ξ_C penalizes representational non-invariance in realization selection.
The empirical analogue is test-invariance:
E_C ≈_op E′_C ⇒ χ_C(E_C) = χ_C(E′_C)
Thus adversarial exposure inherits the same discipline that canonical CBR imposes on realization. The theory may not select realization channels by representational accident, and it may not classify empirical tests by representational accident.
This makes the empirical side internally CBR-like rather than externally methodological.
8.7 Description-Dependence Failure Modes
A proposed empirical CBR claim fails test-invariance if its verdict changes because of any of the following:
post-hoc reparameterization of η,
relabelling of nuisance as signal,
relabelling of signal as nuisance,
choice of favorable baseline decomposition,
choice of favorable rival-model parametrization,
changing coordinate representation of the same observable,
selective use of an equivalent data partition,
or reclassification of the same residual under a different notation.
These failures do not necessarily show CBR is false. They show the empirical instantiation is inadmissible.
8.8 Section Result
This section establishes that CBR exposure must be invariant under operationally equivalent descriptions.
The result is:
E_C ≈_op E′_C ⇒ χ_C(E_C) = χ_C(E′_C)
The exposure verdict belongs to the operational test class [E_C]_op, not to a preferred description.
This closes the description-dependence loophole and prevents CBR support or falsification from depending on presentation choices.
9. Critical-Regime Fixity: η and η_c
CBR’s empirical exposure depends on accessibility. The canonical paper introduces η as an operational accessibility parameter and η_c as the critical accessibility regime where accessibility-sensitive realization behavior may become empirically visible. It also ties the theory’s failure condition to behavior across the accessibility-critical regime under detectability-valid conditions.
This makes η and η_c central. They are not auxiliary plotting choices. They are the empirical handles by which Λ_C becomes testable.
If η is not independently calibrated, the accessibility axis can be shaped after the fact. If η_c is not fixed before data, the critical regime can be moved to whatever residual appears. Either failure destroys adversarial exposure.
This section therefore imposes two rules:
η must be independently calibrated.
η_c must be derived, bounded, or pre-registered before confirmatory data inspection.
9.1 η as the Empirical Handle on Λ_C
The canonical burden functional is:
ℛ_C = αΞ_C + βΩ_C + γΛ_C
The Λ_C term is the accessibility-consistency burden. In an accessibility-sensitive experiment, η is the operational variable through which Λ_C becomes empirically visible.
Therefore η is not merely a horizontal axis for plotting V(η). It is the empirical representation of accessibility structure.
Let s denote the directly controlled laboratory setting. The experiment controls s, but the CBR prediction is stated over η. Therefore a calibration map is required:
η = g(s)
The map g must be fixed independently of the residuals used to claim CBR support or falsification.
9.2 Independent Calibration Rule
The calibration map g is admissible only if it is fixed using evidence external to the confirmatory residuals.
Acceptable sources include:
independent record-accessibility measurements,
which-path mutual-information estimates,
record-state tomography,
detector-accessibility audits,
calibration-only control runs,
blinded calibration partitions,
and pre-registered simulations tied to independently measured apparatus parameters.
Unacceptable sources include:
moving η_c to match a residual,
stretching η after seeing the visibility curve,
using the residual itself to infer accessibility,
changing g after the CBR prediction fails,
or treating a failed prediction as evidence of miscalibration without independent support.
The rule is:
η may be calibrated from accessibility evidence, not from the anomaly it is supposed to explain.
9.3 The Axis-Warping Problem
If η = g(s) is adjustable after data inspection, then the same observed residual can be moved into or out of the critical regime. This permits target movement without appearing to change the theory.
Axis warping is especially dangerous because it can masquerade as calibration refinement. A post-data change to g may be presented as an improved accessibility estimate, while functionally it relocates the empirical target.
Therefore adversarial closure requires a distinction between admissible calibration refinement and inadmissible axis warping.
A calibration refinement is admissible only if it is justified by independent calibration evidence and applied before confirmatory verdict assignment.
An axis warp is inadmissible if it is motivated by the residuals used to claim support, avoid falsification, or change verdict status.
9.4 Three Levels of η_c Fixity
The critical regime η_c may be fixed at three levels of strength.
Strong Form: Derived η_c
The strongest form derives η_c from the burden geometry and protocol structure:
η_c = f(Ξ_C, Ω_C, Λ_C, protocol structure)
This is the ideal form because it makes the critical regime theory-determined.
Moderate Form: Bounded η_c
The moderate form bounds η_c inside a protocol-derived interval:
η_c ∈ [η_−, η_+]
The critical interval is then:
I_c = [η_− − δ, η_+ + δ]
This is admissible if the interval is fixed before data and narrow enough to create real empirical risk.
Weak but Admissible Form: Pre-Registered η_c Window
The weakest admissible form pre-registers a finite critical window:
η_c ∈ I_pre
This is acceptable only if the window is fixed before confirmatory data inspection and cannot be moved after the result is known.
The hierarchy is:
derived η_c > bounded η_c > pre-registered η_c window > post-data η_c movement
Only the first three are admissible. The last is not.
9.5 Critical-Regime Fixity Theorem
Theorem 5: Critical-Regime Fixity Theorem
A CBR accessibility test is empirically admissible only if η_c, or a bounded critical interval containing η_c, is derived, bounded, or pre-registered before confirmatory data inspection.
If η_c is selected, moved, widened, narrowed, or reinterpreted after residual inspection in a way that changes the verdict, then:
χ_C([E_C]_op) = inadmissible
9.6 Proof
The predicted CBR signature L_CBR is localized in or around the critical accessibility regime I_c. Therefore the empirical verdict depends on whether the predicted signature appears in that region.
If η_c is selected after data inspection, any localized residual can be made CBR-relevant by placing η_c near it. Conversely, any failed prediction can be avoided by moving η_c away from the tested region or widening the critical interval until the failure condition no longer applies.
In either case, the target is not fixed before the test. The exposure map χ_C is no longer assigning verdicts under predeclared rules. It is being altered in response to the outcome.
Therefore post-data movement of η_c destroys empirical admissibility.
9.7 Corollary: No Moving Critical Windows
If a proposed CBR test changes η_c, I_c, or δ after the data are inspected, the original test loses confirmatory status.
The revised test may be proposed as:
E′_C
but it does not rescue the original:
E_C
Thus:
post-data movement of η_c, I_c, or δ ⇒ E′_C ≠ E_C
9.8 Corollary: η_c Must Create Risk
A pre-registered η_c window is admissible only if it is narrow enough to create a real possibility of failure.
If the window is so broad that almost any residual counts as inside the critical regime, then the test is not adversarially exposed.
Thus η_c fixity requires not merely pre-registration, but risk-bearing pre-registration.
9.9 Relation to Strong-Null Failure
The strong-null condition depends on η_c because the null must be evaluated across the critical regime. A null result is falsifying only if the predicted signature fails to appear in I_c under conditions where the experiment had adequate sensitivity and nuisance bounds remained valid.
Therefore strong-null failure requires:
η independently calibrated,
η_c fixed,
I_c specified,
δ fixed,
ε detectable,
τ declared,
and Δ_N valid across I_c.
If these conditions are missing, the result cannot fairly falsify CBR. It is inadmissible or inconclusive.
9.10 Section Result
This section establishes that η and η_c are not adjustable empirical conveniences. They are verdict-bearing structures.
The accessibility axis η must be independently calibrated.
The critical regime η_c must be derived, bounded, or pre-registered before data.
The critical interval I_c must be fixed strongly enough to create real empirical risk.
Post-data movement of η, η_c, I_c, or δ creates a new instantiation rather than rescuing the old one.
The result is:
No independent η, no admissible accessibility test.
No fixed η_c, no valid critical-regime verdict.
This closes the target-movement loophole at the accessibility level.
10. Hostile Nuisance and Rival-Model Library
A CBR-supportive result cannot be established merely by rejecting a smooth baseline. That would be too weak. A localized residual near the accessibility-critical regime may be real and still not be a CBR realization signature. It may arise from baseline curvature, apparatus drift, detector saturation, imperfect erasure, source instability, η-axis miscalibration, reconstruction bias, or a generic localized anomaly unrelated to CBR.
For this reason, adversarial exposure requires a hostile comparison class. The CBR model must be tested not only against the standard baseline but also against explicit non-CBR rivals capable of producing the same apparent feature.
The governing rule is:
CBR must defeat rival explanations, not merely the null.
This section defines the baseline class B, nuisance class N, nuisance envelope Δ_N, rival library M_rival, and rival-resistance condition required for a CBR-supportive verdict.
10.1 Baseline Class B
Let B denote the declared class of standard quantum/decoherence baseline models for the observable V(η).
A baseline model may be written:
V_B(η; θ_B)
where θ_B denotes baseline parameters.
The baseline class B must be fixed before confirmatory analysis. It must be broad enough to include legitimate standard behavior, but not so broad that it can absorb arbitrary local structure.
This creates two symmetric failure modes.
If B is too narrow, ordinary standard behavior may be misclassified as a CBR deviation.
If B is too broad, a genuine CBR-like deviation may be absorbed into baseline flexibility.
Therefore B must satisfy a bounded-flexibility condition:
B may represent validated standard behavior, but may not contain arbitrary localized features unless those features are independently justified before data.
A baseline cannot be made hostile or permissive after the result is known. A post-data expansion or contraction of B changes the empirical instantiation.
Thus:
post-data change of B ⇒ E′_C ≠ E_C
10.2 Nuisance Class N
Let N denote the declared class of non-CBR apparatus, environmental, calibration, and analysis effects.
A nuisance contribution may be written:
N(η; θ_N)
The nuisance envelope is:
Δ_N(η) = sup{|N(η; θ_N)| : N ∈ N}
The nuisance envelope must be fixed before confirmatory interpretation and justified by independent apparatus characterization, calibration data, control runs, or pre-registered error modeling.
The nuisance class should include, where relevant:
phase drift,
timing jitter,
detector inefficiency,
detector saturation,
dark counts,
loss imbalance,
thermal instability,
source coherence drift,
imperfect erasure,
alignment drift,
η-calibration uncertainty,
finite sampling error,
post-selection bias,
and reconstruction bias.
The nuisance class has two roles.
First, it protects CBR from false support. A residual inside the nuisance envelope is not CBR evidence.
Second, it protects CBR from false falsification. A null obtained under uncontrolled nuisance conditions is not a valid strong null.
A CBR-supportive residual must therefore satisfy:
|V_obs(η) − V_B(η)| > Δ_N(η) + τ
inside the critical region I_c, and it must match the predeclared L_CBR.
If the residual does not exceed Δ_N + τ, the result is not CBR-supportive.
10.3 Nuisance Boundedness
Definition: Bounded Nuisance Class
A nuisance class N is bounded if Δ_N(η) is finite, independently justified, and fixed before confirmatory interpretation across the relevant η-domain, especially inside I_c.
If N is not bounded, then the exposure map χ_C cannot be well-defined.
An unbounded nuisance class can be used to dismiss any residual.
An underdeclared nuisance class can be used to inflate ordinary artifacts into CBR support.
Therefore adversarial closure requires:
N fixed, Δ_N bounded, and nuisance justification external to the CBR residual.
10.4 Rival Library M_rival
Let M_rival denote the declared class of non-CBR models capable of mimicking a CBR-like accessibility signature.
The rival library must be declared before confirmatory analysis. It cannot be assembled only after a residual appears, and it cannot be selectively weakened to make CBR easier to support.
A hostile minimal rival library contains the following models.
M₀: Smooth baseline plus nuisance
V(η) = V_B(η) + N(η)
This is the ordinary standard comparator.
M₁: CBR accessibility model
V(η) = V_B(η) + L_CBR(η) + N(η)
This is the CBR model under test.
M₂: Baseline curvature model
V(η) = V_curve(η) + N(η)
This rival tests whether the alleged signature is merely unmodeled smooth or high-curvature baseline structure.
M₃: Phase-drift model
V(η) = V_B(η) + A_phase(η) + N(η)
This rival tests whether phase instability can mimic the residual.
M₄: Detector-saturation model
V(η) = V_B(η) + A_sat(η) + N(η)
This rival tests whether nonlinear detector response can produce the apparent feature.
M₅: Imperfect-erasure model
V(η) = V_B(η) + A_erase(η) + N(η)
This rival tests whether incomplete erasure or residual which-path information explains the signal.
M₆: Source-coherence-drift model
V(η) = V_B(η) + A_source(η) + N(η)
This rival tests whether source instability or coherence drift produces a localized residual.
M₇: η-axis miscalibration model
V(η) = V_B(f(η)) + N(η)
This rival tests whether the result depends on an incorrect accessibility calibration.
M₈: Generic localized anomaly model
V(η) = V_B(η) + K(η) + N(η)
This rival tests whether the observed feature is merely a localized anomaly without CBR-specific structure.
M₉: Reconstruction-bias model
V(η) = V_B(η) + R_rec(η) + N(η)
This rival tests whether the analysis or reconstruction pipeline generates the feature.
The rival library may be expanded for a specific platform. It may not be weakened after data inspection.
10.5 Model M₁ Is Not Privileged by Default
The CBR model M₁ is a member of the rival library. It is not automatically preferred because it is the theory of interest.
A CBR-supportive result requires more than:
M₁ fits D
It requires:
M₁ fits D better than every declared non-CBR rival by the predeclared margin κ
This distinction is essential. A flexible CBR term L_CBR could fit a residual. But unless that residual is predeclared, nuisance-separated, and rival-resistant, the fit does not identify CBR.
The burden is therefore:
CBR must win adversarially, not merely descriptively.
10.6 Rival-Resistance Condition
Let D be the confirmatory dataset.
Let S(M; D) be the predeclared model score for model M on D.
Let κ be the predeclared separation margin.
The CBR model M₁ is rival-resistant only if:
S(M₁; D) > S(M_j; D) + κ
for every declared rival:
M_j ∈ M_rival, j ≠ 1
The scoring rule S may be Bayesian, likelihood-based, information-criterion-based, cross-validation-based, or otherwise justified before data. The exact statistical implementation is not fixed by CBR. What is fixed is the requirement that the rule be declared before confirmatory interpretation.
Equivalent forms include:
Pr(M₁ | D) ≫ Pr(M_j | D)
or:
IC(M_j) − IC(M₁) > κ
for every declared non-CBR rival.
The adversarial rule is:
No rival resistance, no CBR support.
10.7 Nuisance-Separation Condition
A CBR-supportive residual must satisfy three conditions simultaneously.
First, it must exceed the nuisance envelope:
|V_obs(η) − V_B(η)| > Δ_N(η) + τ
inside I_c.
Second, it must match the predeclared CBR signature L_CBR in location, width, sign, magnitude, morphology, and relation to Λ_C.
Third, it must defeat the declared rival library by at least κ.
A residual satisfying only the first condition is an anomaly.
A residual satisfying the first and second conditions is a CBR-shaped anomaly.
A residual satisfying all three conditions is a CBR-supportive result.
This distinction prevents the theory from treating every unexpected feature as support.
10.8 Failure Modes of Rival Separation
A proposed support claim fails rival separation if any of the following occurs:
the rival library is declared after the residual is observed,
the rival library omits obvious artifact classes,
the nuisance envelope is expanded or contracted after data,
the CBR model wins only against an oversimplified baseline,
the alleged signature is equally fit by η-axis miscalibration,
the alleged signature is equally fit by generic localized anomaly,
the effect appears in negative-control regions,
or the model-selection rule is chosen after the result is known.
Any of these failures makes the support claim inadmissible or non-CBR-specific.
10.9 Section Result
This section establishes that empirical CBR support requires hostile model separation.
The result is:
A CBR-supportive residual must exceed nuisance, match L_CBR, and defeat M_rival.
Rejecting a smooth null is not enough.
A localized anomaly is not enough.
A CBR-shaped residual is not enough.
Support requires rival-resistant identification.
This prepares the Anomaly-Absorption Theorem.
11. Anomaly-Absorption Theorem
The strongest threat to empirical CBR support is anomaly absorption. A residual may appear where CBR predicted a signature, but if the residual can be absorbed by non-CBR models, it does not identify CBR.
This theorem formalizes that principle.
The issue is not whether the residual is real. It may be real. The issue is whether the residual is CBR-specific.
A result supports CBR only if the CBR model is not observationally replaceable, within tolerance, by a non-CBR absorption model.
11.1 Absorption Class
Let Q denote the non-CBR absorption class.
Q includes models capable of reproducing the apparent CBR signature without invoking CBR realization structure.
At minimum, Q contains the non-CBR rivals in M_rival:
baseline curvature,
phase drift,
detector saturation,
imperfect erasure,
source coherence drift,
η-axis miscalibration,
generic localized anomaly,
reconstruction bias,
and baseline plus nuisance.
A member Q ∈ Q may take forms such as:
Q₀(η) = V_B(η) + N(η)
Q₁(η) = V_curve(η) + N(η)
Q₂(η) = V_B(η) + A_phase(η) + N(η)
Q₃(η) = V_B(η) + A_sat(η) + N(η)
Q₄(η) = V_B(η) + A_erase(η) + N(η)
Q₅(η) = V_B(η) + A_source(η) + N(η)
Q₆(η) = V_B(f(η)) + N(η)
Q₇(η) = V_B(η) + K(η) + N(η)
Q₈(η) = V_B(η) + R_rec(η) + N(η)
The exact platform may require additional Q models. The minimum demand is that Q include all credible non-CBR mechanisms capable of producing a localized accessibility-correlated feature.
11.2 CBR Model Under Test
The CBR accessibility model has the form:
V_CBR(η) = V_B(η) + L_CBR(η) + N(η)
where:
V_B is the baseline class,
L_CBR is the predeclared CBR accessibility signature,
N is the nuisance contribution,
and η lies in the predeclared critical interval:
I_c
The claim of support is not that V_CBR can fit the data. The claim is that V_CBR fits in a CBR-specific way that cannot be absorbed by Q.
11.3 Definition: Absorbability
The CBR signature is absorbable if there exists a non-CBR absorption model Q ∈ Q such that:
||V_CBR(η) − Q(η)|| over η ∈ I_c ≤ τ
Equivalently, the CBR prediction is empirically indistinguishable from a non-CBR rival within the detection threshold τ over the critical interval.
If the signature is absorbable, then it is not CBR-identifying.
11.4 Theorem 5: Anomaly-Absorption Theorem
A localized deviation in V_obs(η) supports CBR only if the predeclared CBR signature cannot be absorbed by any admissible non-CBR model in Q within τ over the critical interval I_c.
Formally, CBR support requires:
inf{||V_CBR(η) − Q(η)|| over η ∈ I_c : Q ∈ Q} > τ
If instead:
inf{||V_CBR(η) − Q(η)|| over η ∈ I_c : Q ∈ Q} ≤ τ
then the alleged CBR signature is absorbable and does not identify CBR.
11.5 Proof
Suppose:
inf{||V_CBR(η) − Q(η)|| over η ∈ I_c : Q ∈ Q} ≤ τ
Then there exists at least one admissible non-CBR absorption model Q that reproduces the CBR-predicted behavior within the experiment’s detection threshold over the critical interval.
In that case, the observable record cannot distinguish between the CBR model and the non-CBR rival. The residual may still be present, and it may still be localized, but its attribution to CBR is not warranted.
Empirical support requires identification, not merely fit. Since the CBR term is observationally replaceable by a non-CBR absorption model within τ, the result fails CBR-specific identification.
Therefore a CBR-supportive verdict requires non-absorption:
inf{||V_CBR(η) − Q(η)|| over η ∈ I_c : Q ∈ Q} > τ
11.6 Corollary 1: Surprise Is Not Support
A surprising residual is not CBR support.
A localized residual is not CBR support.
A residual near η_c is not CBR support.
A residual matching the rough shape of L_CBR is not yet CBR support.
It becomes CBR-supportive only if it is predeclared, nuisance-separated, and non-absorbable by Q.
11.7 Corollary 2: Baseline Rejection Is Not Support
Rejecting M₀, the smooth baseline plus nuisance model, does not by itself support CBR.
A rejected baseline may indicate:
unmodeled curvature,
apparatus drift,
η-axis error,
source instability,
reconstruction artifact,
or a generic anomaly.
CBR support requires defeating the hostile rival library, not merely defeating the simplest null.
11.8 Corollary 3: Generic Anomaly Is Not CBR
If the data are better explained by:
V(η) = V_B(η) + K(η) + N(η)
where K(η) is a generic localized anomaly with no CBR-specific relation to Λ_C, then the result is not CBR-supportive.
The anomaly may justify further investigation, but it does not identify CBR.
11.9 Corollary 4: η-Axis Miscalibration Defeats Identification
If the alleged CBR signature is absorbable by an η-axis miscalibration model:
V(η) = V_B(f(η)) + N(η)
then the result is not CBR-supportive.
This is especially important because η is the empirical handle on Λ_C. If the accessibility axis is not independently secured, then the CBR signature is not identified.
11.10 Relation to Nuisance Separation
Nuisance separation and anomaly absorption are related but not identical.
Nuisance separation asks whether the residual exceeds the declared nuisance envelope:
|V_obs(η) − V_B(η)| > Δ_N(η) + τ
Anomaly absorption asks whether a non-CBR rival can reproduce the residual within τ.
A residual may exceed nuisance and still be absorbable by a rival model.
Therefore both tests are required.
The CBR support path is:
exceed nuisance → match L_CBR → defeat absorption
Skipping the final step leaves the result non-CBR-specific.
11.11 Section Result
This section establishes the non-absorption condition for CBR support.
The result is:
A residual is CBR-supportive only if no admissible non-CBR rival absorbs the predicted CBR signature within τ over I_c.
This closes the anomaly-absorption loophole.
CBR cannot claim a residual merely because it is unexpected, localized, or near η_c.
CBR must show that the residual is specifically its own.
12. No-Rescue Falsification
A theory candidate is not genuinely exposed if it can revise the tested commitments after failure and treat the revised version as though the original test had not failed.
CBR must allow revision at the program level. Scientific theories can and should be revised. But revision must not be retroactive. Once an empirical instantiation E_C is fixed and tested under its own admissibility and strong-null conditions, that instantiation either survives, fails, or is inadmissible.
If it fails, changing the target afterward does not rescue it. It defines a new instantiation.
This section formalizes that rule.
12.1 Fixed Empirical Instantiation
An empirical instantiation E_C includes:
π(E_C),
𝒜(C),
ℛ_C,
η,
g,
η_c,
I_c,
L_CBR,
B,
N,
Δ_N,
M_rival,
V,
D,
S,
κ,
τ,
and χ_C.
These are not presentation details. They are verdict-bearing commitments.
Once E_C is admitted into confirmatory testing, changes to these commitments change the test.
12.2 Strong-Null Failure
A strong-null failure occurs when:
E_C ∈ Emp_adm(C),
π(E_C) ∈ 𝒜(C),
χ_C is invariant under ≈_op,
η is independently calibrated,
η_c and I_c are fixed,
L_CBR is restricted,
B is validated,
N and Δ_N remain valid,
M_rival is declared,
S, κ, and τ are fixed,
the experiment has power to detect ε,
I_c is adequately sampled,
and the observed behavior remains within the validated baseline-plus-nuisance class across I_c with no strong-form or weak-form CBR accessibility signature beyond tolerance.
Under those conditions:
χ_C([E_C]_op) = falsifying
The scope of the falsification depends on the scope of E_C. It falsifies the tested empirical instantiation. It may, under broader repeated success of the strong null across the declared protocol family, falsify the present canonical accessibility model. It does not automatically eliminate every possible future CBR revision.
12.3 The No-Rescue Rule
The no-rescue rule states:
A failed admissible E_C cannot be rescued by post-failure modification of verdict-bearing commitments.
The following changes define a new empirical instantiation E′_C:
moving η_c,
widening or narrowing I_c,
changing δ,
changing γ or any burden coefficient,
changing L_CBR,
changing B,
changing N,
changing Δ_N,
adding or removing rival models,
changing S,
changing κ,
changing τ,
changing χ_C,
changing the admissibility filtration,
or redefining π(E_C).
Thus:
post-failure modification of verdict-bearing structure ⇒ E′_C ≠ E_C
The revised instantiation may be proposed. It may even be scientifically valuable. But it does not erase the verdict against the original instantiation.
12.4 Theorem 6: No-Rescue Theorem
If E_C is empirically admissible and fails under its own strong-null condition, then any post-failure modification of η_c, γ, L_CBR, B, N, Δ_N, M_rival, S, κ, τ, χ_C, π(E_C), or the admissibility filtration defines a new empirical instantiation E′_C rather than rescuing E_C.
The failed E_C remains failed.
12.5 Proof
Empirical admissibility requires that the target, admissible class, calibration, critical regime, signature, baseline, nuisance envelope, rival library, thresholds, score rule, and verdict map be fixed before confirmatory interpretation.
A strong-null failure is evaluated against those fixed commitments.
Suppose E_C fails under its own strong-null condition. If a verdict-bearing commitment is then changed, the object being evaluated is no longer the same instantiation. The new object differs in target, prediction, nuisance structure, rival structure, decision rule, or failure condition.
Therefore the post-failure modification cannot alter the original verdict. It can only define a new empirical instantiation E′_C.
Thus a failed E_C remains failed.
12.6 Corollary 1: Revision Is Allowed but Not Retroactive
CBR may revise after failure.
However, revision must be explicit.
A revised model must declare:
new π(E_C), if the target changes,
new 𝒜(C), if admissibility changes,
new η or η_c treatment, if accessibility changes,
new L_CBR, if the signature changes,
new B, N, or Δ_N, if comparison structure changes,
new M_rival, if rivals change,
new S, κ, or τ, if verdict rules change,
and new χ_C, if the exposure map changes.
The revised proposal must then re-enter the adversarial exposure process.
It cannot be counted as the original test surviving.
12.7 Corollary 2: Post-Hoc Narrowing Is Not Rescue
If CBR predicts a signature over a declared critical interval I_c and the signature fails to appear, the test cannot be rescued by narrowing I_c after data to exclude the failed region.
That defines a new E′_C.
The original E_C remains falsified if strong-null conditions were satisfied.
12.8 Corollary 3: Post-Hoc Broadening Is Not Rescue
If CBR predicts a signature over a declared critical interval I_c and the signature appears only outside that interval, the test cannot be rescued by broadening I_c after data to include the residual.
That defines a new E′_C.
The original E_C remains unsupported or falsified according to its predeclared rule.
12.9 Corollary 4: γ Suppression Is Not Rescue
If an accessibility-sensitive CBR instantiation fails, it cannot be rescued by saying after the fact that γ was effectively zero or that Λ_C was inactive, unless that possibility was part of the predeclared model.
If γ is changed after the null, the original E_C remains failed.
A γ-modified model is a new E′_C.
12.10 Corollary 5: Rival-Model Revision Is Not Rescue
If the CBR model fails to defeat the declared rival library, the result cannot be rescued by removing rivals after the fact or redefining them to be less competitive.
Similarly, if an undeclared rival later explains the residual, the original support claim is weakened or invalidated; the proper response is a new adversarial test with the rival included.
12.11 Scoped Failure Levels
No-rescue falsification must be scoped carefully.
Instantiation Failure
The tested empirical instantiation E_C fails.
This is the narrowest failure level.
Canonical-Model Failure
The present canonical accessibility model fails if strong-null failure is reproduced across the declared protocol family under detectability-valid conditions.
This is stronger than one failed instantiation.
Program-Level Revision
A future CBR variant may still be proposed.
But it must restart the adversarial exposure process with a new E′_C and a new χ_C.
This prevents overclaiming while preserving real falsification.
12.12 Section Result
This section establishes no-rescue falsification.
The result is:
A failed admissible E_C remains failed.
Post-failure modification creates:
E′_C ≠ E_C
This closes the revision loophole.
CBR may revise, but it may not retroactively rescue a failed empirical instantiation.
That is the difference between scientific revision and post-hoc protection.
13. Scoped Failure Levels
A theory candidate becomes scientifically serious only when it can fail. But failure must be scoped correctly. If the scope is too narrow, the theory can evade consequence. If the scope is too broad, a single limited test can be misused to dismiss more than it actually tested.
CBR therefore requires a disciplined hierarchy of failure. The result of an empirical test must be assigned to the proper level: instantiation failure, canonical-model failure, or program-level revision. These are not interchangeable.
The adversarial closure standard is:
Failure must be real, but never over-scoped.
A failed empirical instantiation must remain failed. A failed canonical accessibility model must not be protected by relabeling. But a failure of one tested instantiation should not be exaggerated into the refutation of every logically possible future CBR-like theory.
This section defines the scope rules.
13.1 Instantiation Failure
An empirical instantiation E_C fails when it is empirically admissible, satisfies the strong-null preconditions, and the predicted CBR signature does not appear under its own fixed verdict rule.
Formally, instantiation failure occurs when:
E_C ∈ Emp_adm(C)
π(E_C) ∈ 𝒜(C)
χ_C is invariant on [E_C]_op
and the strong-null condition for that E_C is satisfied.
Then:
χ_C([E_C]_op) = falsifying
This verdict applies to the tested empirical instantiation.
It means that the specific package consisting of 𝒜(C), ℛ_C, η, η_c, I_c, L_CBR, B, N, Δ_N, M_rival, S, κ, τ, and χ_C has failed.
Instantiation failure is narrow, but it is real. It cannot be erased by saying that CBR in some broader sense remains possible. The tested object failed.
13.2 Canonical-Model Failure
Canonical-model failure is stronger than instantiation failure.
It occurs when the present canonical accessibility model fails across the declared protocol family under detectability-valid conditions.
The canonical accessibility model includes:
the canonical law form,
the restricted admissible class,
the Λ_C accessibility burden,
the operational accessibility parameter η,
the critical-regime structure η_c or I_c,
the predicted accessibility signature L_CBR,
the designated protocol family,
the nuisance-separation requirement,
and the strong-null failure condition.
A single failed instantiation may falsify only that instantiation. But repeated strong-null failures across the declared accessibility-sensitive protocol family would count against the present canonical accessibility model itself.
The standard is: If the declared protocol family repeatedly exhibits only validated baseline-class behavior across the accessibility-critical regime under detectability-valid conditions, then the present canonical accessibility model fails.
This is consistent with the canonical closure paper’s own strong-null posture: if validated baseline-class behavior persists across the accessibility-critical regime under declared detectability conditions, the instantiated canonical model is false.
Canonical-model failure is not a vague disappointment. It is the failure of the present canonical accessibility-signature architecture.
13.3 Program-Level Revision
Program-level revision is broader still.
If an instantiation fails, or if the present canonical accessibility model fails, a future CBR-like theory may still be proposed. But it cannot be treated as the same empirical object. It must restart the adversarial closure process.
A program-level revision must declare:
a revised context structure, if C changes,
a revised admissible class, if 𝒜(C) changes,
a revised burden structure, if ℛ_C changes,
a revised accessibility parameter, if η changes,
a revised critical regime, if η_c or I_c changes,
a revised signature, if L_CBR changes,
a revised nuisance or rival structure, if B, N, Δ_N, or M_rival change,
a revised exposure map, if χ_C changes,
and a revised failure criterion, if the strong-null condition changes.
Such a revision may be scientifically legitimate. But it is not retroactive survival of the failed object.
The rule is: Revision is allowed, but revision restarts exposure.
13.4 Failure-Scope Theorem
Theorem 7: Failure-Scope Theorem
Let E_C be an empirically admissible CBR instantiation. If E_C fails under its own strong-null condition, then the falsification applies at least to E_C. It applies to the present canonical accessibility model only if the failure is reproduced across the declared protocol family under detectability-valid conditions. It applies to the entire CBR research program only if no revised admissible realization-law structure can be stated without violating the adversarial closure conditions.
Proof
The empirical verdict χ_C([E_C]_op) is defined on a specific operational equivalence class of empirical instantiations. Therefore a strong-null failure directly falsifies that class.
The canonical accessibility model is a broader object than a single instantiation. It is falsified only when the declared model-level accessibility burden fails across the relevant protocol family under valid detectability and nuisance conditions.
The total research program is broader still. It includes the possibility of future revised structures. Such revisions are not automatically invalid, but each revision defines a new object requiring new admissibility, calibration, exposure, rival-comparison, and failure conditions.
Therefore failure propagates only as far as the tested commitments justify.
13.5 Corollary: No Under-Scoping
A failed E_C cannot be dismissed as irrelevant merely because the broader program may continue.
If E_C is empirically admissible and fails under strong-null conditions, then E_C is falsified.
The result cannot be softened into “inconclusive” unless an admissibility or detectability condition actually failed.
13.6 Corollary: No Over-Scoping
A failed E_C does not automatically falsify every possible future CBR-like theory.
A broader conclusion requires broader exposure.
This is not weakness. It is proper scientific scoping.
13.7 Corollary: No Revision Without Reset
A revised CBR proposal after failure must define a new E′_C and a new exposure process.
The revised proposal must not be presented as the original E_C surviving.
Thus:
failed E_C + post-failure modification = new E′_C, not rescued E_C
13.8 Section Result
This section establishes the hierarchy of failure:
Instantiation failure applies to the tested E_C.
Canonical-model failure applies to the present accessibility-signature architecture across its declared protocol family.
Program-level revision remains possible only by restarting adversarial exposure.
This gives CBR the right kind of vulnerability: real enough to matter, scoped enough to be fair, and strict enough to prevent rescue by ambiguity.
14. Adversarial Decision Procedure
The exposure map χ_C must be operational, not merely symbolic. A valid CBR test therefore proceeds through a fixed decision sequence. This sequence is part of the empirical instantiation itself. It must be declared before confirmatory interpretation.
The procedure is ordered. Admissibility questions come first. Only after the test passes the admissibility gates may it enter the support path or the strong-null path.
This ordering prevents two errors.
First, it prevents weak or underdefined experiments from being counted as support.
Second, it prevents weak or underpowered nulls from being counted as falsification.
The decision procedure is therefore the operational implementation of:
χ_C : Emp_adm(C) / ≈_op → {supportive, falsifying, inadmissible}
14.1 Context Gate
The first gate asks whether C is physically specified.
The test must identify the physical system, apparatus, record-bearing structures, accessibility-relevant degrees of freedom, protocol family, timing relations, and primary observable V(η).
If C is not physically specified, the verdict is:
inadmissible
A CBR test cannot be evaluated without a determinate context because 𝒜(C), η, η_c, nuisance structure, and the strong-null condition all depend on C.
14.2 Admissible-Class Gate
The second gate asks whether 𝒜(C) has been constructed by the filtration:
Ch(C) → F₁(C) → F₂(C) → F₃(C) → F₄(C) → F₅(C) → F₆(C) → 𝒜(C)
with:
𝒜(C) = F₆(C) / ≈_op
If the filtration trace is missing, the verdict is:
inadmissible
A named admissible class is not enough. The test must show how candidate channels survive the exclusion of dynamical leakage, representational dependence, record incoherence, accessibility arbitrariness, probability insertion, and empirical idleness.
14.3 Projection Gate
The third gate asks whether the empirical instantiation has a formal target π(E_C) and whether:
π(E_C) ∈ 𝒜(C)
If no such target is defined, or if the target does not belong to 𝒜(C), the verdict is:
inadmissible
This prevents a test from claiming to evaluate CBR while failing to target a canonically admissible CBR channel or channel-family.
14.4 Accessibility Gate
The fourth gate asks whether η is independently calibrated.
The calibration map:
η = g(s)
must be fixed from accessibility evidence external to the residuals used for CBR classification.
If η is inferred from the same anomaly it is later used to explain, the verdict is:
inadmissible
No independent η means no admissible accessibility test.
14.5 Critical-Regime Gate
The fifth gate asks whether η_c, or a bounded critical interval containing η_c, is derived, bounded, or pre-registered before confirmatory data inspection.
If η_c is selected, moved, widened, narrowed, or reinterpreted after residual inspection in a verdict-changing way, the verdict is:
inadmissible
A movable critical regime would permit target movement.
14.6 Signature Gate
The sixth gate asks whether L_CBR is restricted before data.
The predicted signature must be fixed in:
location,
width,
sign,
minimum magnitude,
morphology,
critical interval,
relation to Λ_C,
and detection threshold.
If L_CBR is unrestricted, the verdict is:
inadmissible
An unrestricted signature is not a prediction. It is an anomaly receptacle.
14.7 Burden-Parameter Gate
The seventh gate asks whether α, β, and γ are fixed before data, or varied only within predeclared ranges.
If any burden coefficient is adjusted after data to amplify a residual, suppress a null, or reinterpret accessibility relevance, the verdict is:
inadmissible
The burden coefficients belong to the theory-level structure. They are not post-hoc fit knobs.
14.8 Baseline-and-Nuisance Gate
The eighth gate asks whether B, N, and Δ_N are fixed before confirmatory interpretation.
If the baseline class is changed after data, the verdict is:
inadmissible
If the nuisance class is expanded after data to dismiss a failed signal, the verdict is:
inadmissible
If the nuisance class is narrowed after data to inflate a residual into support, the verdict is:
inadmissible
Baseline and nuisance structure must be fixed before the result is known.
14.9 Rival-Library Gate
The ninth gate asks whether M_rival is declared before data and includes credible non-CBR mechanisms capable of mimicking the alleged signal.
If obvious rivals are absent, or if the rival library is assembled only after the result is seen, the verdict is:
inadmissible
CBR cannot claim support merely by defeating a weak null. It must defeat hostile alternatives.
14.10 Verdict-Rule Gate
The tenth gate asks whether S, κ, and τ are fixed before data.
S is the model-scoring rule.
κ is the model-separation margin.
τ is the detection or resolution threshold.
If any of these are chosen after outcome inspection, the verdict is:
inadmissible
The verdict rule must not be selected to favor the observed result.
14.11 Test-Invariance Gate
The eleventh gate asks whether χ_C is invariant under operationally equivalent descriptions.
If E_C ≈_op E′_C, then a valid exposure map must satisfy:
χ_C(E_C) = χ_C(E′_C)
If equivalent descriptions yield different verdicts, the verdict is:
inadmissible
The test cannot depend on notation, parametrization, or preferred decomposition.
14.12 Power Gate
The twelfth gate asks whether the experiment has sufficient power to detect ε inside I_c.
If the experiment could not have detected the predicted effect, then a null result cannot falsify the test.
The verdict is:
inadmissible
or, if the experiment is explicitly exploratory:
exploratory but not confirmatory
A powerless null is not a strong null.
14.13 Support Path
Only after all admissibility gates are passed may the test enter the support path.
The first support question is whether the predicted L_CBR appears inside I_c and exceeds the nuisance envelope by the declared threshold:
|V_obs(η) − V_B(η)| > Δ_N(η) + τ
If no such feature appears, the test leaves the support path and enters the strong-null path.
If the feature appears, the next question is whether the feature matches the predeclared L_CBR in location, width, sign, magnitude, morphology, and relation to Λ_C.
If it does not, the result is not CBR-supportive.
If it does, the final support question is whether the CBR model M₁ defeats every declared rival by at least κ.
If it does, the verdict is:
supportive
If it does not, the result is not CBR-supportive. It is a rival-absorbed anomaly, a non-CBR anomaly, or an inadmissible support claim.
14.14 Strong-Null Path
If the predicted L_CBR does not appear, the result enters the strong-null path.
The absence of L_CBR falsifies the tested instantiation only if the strong-null conditions are satisfied.
Those conditions are:
η was independently calibrated,
η_c and I_c were fixed,
I_c was adequately sampled,
B was validated,
N and Δ_N remained valid,
M_rival was declared,
the experiment had power to detect ε,
S, κ, and τ were fixed,
and the observed behavior remained inside the validated baseline-plus-nuisance envelope across I_c.
If all of these conditions hold, the verdict is:
falsifying
If they do not hold, the result is not a valid falsification. It is inadmissible or exploratory.
14.15 No-Rescue Path
If the verdict is falsifying, the original E_C remains failed.
If one later changes η_c, I_c, γ, L_CBR, B, N, Δ_N, M_rival, S, κ, τ, χ_C, π(E_C), or 𝒜(C), then the revised structure is a new empirical instantiation:
E′_C ≠ E_C
The revised instantiation may be proposed and tested, but it does not rescue the original.
The no-rescue rule is:
Failure under fixed admissible conditions is not retroactively undone by changing those conditions.
14.16 Section Result
This section operationalizes χ_C as a decision procedure.
A CBR empirical claim must first pass the admissibility gates. Only then may it enter the support path or strong-null path.
The procedure prevents:
support without admissibility,
support without rival defeat,
falsification without sensitivity,
falsification without calibration,
and revision without reset.
The result is a verdict sequence strict enough for adversarial review.
15. External Audit Requirements
Adversarial closure requires independent audit. A CBR test cannot claim confirmatory status merely because its authors say the right structures were fixed. The fixation, calibration, nuisance bounds, rival models, and verdict rules must be inspectable by external reviewers.
The external audit is therefore not an optional supplement. It is part of empirical admissibility.
A test that cannot be audited cannot claim adversarially closed status.
This section defines the audit requirements.
15.1 η Calibration Audit
The first audit concerns η.
Auditors must verify that η was calibrated independently of the residuals used for CBR classification.
The audit record must include:
the calibration protocol,
the calibration dataset,
the uncertainty model,
the relation η = g(s),
the allowed η transformations,
and the forbidden post-data adjustments.
The key audit question is:
Was η fixed by accessibility evidence, or by the anomaly it later explained?
If the latter, the test is inadmissible.
15.2 η_c Audit
The second audit concerns η_c and I_c.
Auditors must verify whether η_c was derived, bounded, or pre-registered before confirmatory data inspection.
The audit record must include one of the following:
a burden-geometry derivation,
a protocol-derived interval,
or a time-stamped pre-registration of the critical window.
The audit must also verify that η_c, I_c, and δ were not moved, widened, narrowed, or reinterpreted after residual inspection in a way that changed the verdict.
The key audit question is:
Was the critical regime fixed before the result was known?
If not, the test is inadmissible.
15.3 Admissibility Filtration Audit
The third audit concerns 𝒜(C).
Auditors must be able to reconstruct the filtration:
Ch(C) → F₁(C) → F₂(C) → F₃(C) → F₄(C) → F₅(C) → F₆(C) → 𝒜(C)
They must verify that each filtration stage was applied before data interpretation and that the operational quotient was defined.
The audit must determine whether candidate channels were excluded consistently for dynamical leakage, representational dependence, record incoherence, accessibility arbitrariness, probability insertion, and empirical idleness.
The key audit question is:
Can the admissible class be reconstructed without knowing the outcome?
If not, the test is inadmissible.
15.4 Baseline Class Audit
The fourth audit concerns B.
Auditors must verify that the baseline class was declared before data, justified by standard modeling or control data, and neither too narrow nor too flexible.
The audit must ask whether B could represent legitimate standard quantum/decoherence behavior without absorbing arbitrary localized structure.
The key audit question is:
Was the baseline class a fair comparator rather than a straw null or a post-hoc absorber?
If B was chosen or adjusted after the result, the test is inadmissible.
15.5 Nuisance Envelope Audit
The fifth audit concerns N and Δ_N.
Auditors must verify that the nuisance class and nuisance envelope were fixed before confirmatory interpretation and justified by independent apparatus characterization.
The audit should examine:
phase drift,
timing jitter,
detector inefficiency,
detector saturation,
dark counts,
loss imbalance,
thermal instability,
source coherence drift,
imperfect erasure,
alignment drift,
η-calibration uncertainty,
finite sampling error,
post-selection bias,
and reconstruction bias.
The key audit question is:
Was Δ_N externally justified before the residual was interpreted?
If Δ_N was expanded or narrowed after data, the test is inadmissible.
15.6 Rival Library Audit
The sixth audit concerns M_rival.
Auditors must verify that the rival library was declared before data and included credible non-CBR mechanisms capable of mimicking the alleged signature.
At minimum, the audit must check for rivals involving:
baseline curvature,
phase drift,
detector saturation,
imperfect erasure,
source coherence drift,
η-axis miscalibration,
generic localized anomaly,
and reconstruction bias.
The key audit question is:
Did CBR defeat hostile rivals, or only a weak baseline?
If obvious rivals were omitted, the support claim is not adversarially closed.
15.7 Model-Selection Audit
The seventh audit concerns S, κ, and τ.
Auditors must verify that the scoring rule, model-separation margin, and detection threshold were fixed before data inspection.
The audit must determine whether the chosen rule penalized model flexibility, treated rival models fairly, and avoided post-hoc selection of the metric most favorable to CBR.
The key audit question is:
Was the verdict rule fixed before the verdict was known?
If not, the test is inadmissible.
15.8 Blinding and Held-Out Confirmation Audit
The eighth audit concerns separation between exploration and confirmation.
Auditors must verify that exploratory fitting did not contaminate confirmatory verdict assignment.
Acceptable safeguards include:
blinded analysis,
training-confirmation splits,
held-out datasets,
independent replication runs,
or pre-registered analysis pipelines.
The key audit question is:
Was the confirmatory result genuinely held to pre-fixed rules?
If the same data were used both to tune the model and claim confirmation, the result is exploratory, not confirmatory.
15.9 Positive-Control Recovery Audit
The ninth audit concerns sensitivity.
Auditors must verify that the analysis pipeline could recover a controlled or synthetic effect of size ε inside I_c.
The audit record should include:
injected-signal tests,
recovery rates,
false-negative estimates,
and sensitivity margins.
The key audit question is:
Could the experiment have detected the predicted CBR effect if it were present?
If not, a null is not falsifying.
15.10 Negative-Control Audit
The tenth audit concerns specificity.
Auditors must verify that the alleged CBR-like feature does not also appear where CBR does not predict it.
Negative-control regions should be outside I_c or in accessibility regimes where L_CBR is not predicted.
The key audit question is:
Is the alleged signature specific to the predicted critical regime?
If the same feature appears broadly or in control regions, the result is not CBR-specific.
15.11 No-Rescue Audit
The final audit concerns post-failure revision.
Auditors must verify that if E_C failed under its own strong-null condition, no post-failure change was treated as preserving the original instantiation.
Any change to η_c, I_c, γ, L_CBR, B, N, Δ_N, M_rival, S, κ, τ, χ_C, π(E_C), or 𝒜(C) must be classified as a new E′_C.
The key audit question is:
Was a failed instantiation revised honestly as a new test, or retroactively rescued?
If the latter, adversarial closure fails.
15.12 Section Result
This section establishes that external audit is part of empirical admissibility.
A CBR test must be auditable at the levels of:
η calibration,
η_c fixation,
admissibility filtration,
baseline class,
nuisance envelope,
rival library,
model selection,
blinding or held-out confirmation,
positive-control recovery,
negative-control specificity,
and no-rescue compliance.
The result is:
No auditability, no adversarial closure.
An unauditable CBR claim may be exploratory. It may be suggestive. But it is not a publication-ready confirmatory claim.
16. Protocol-Ready Pre-Registration Standard
Adversarial exposure requires more than a conceptual commitment to pre-registration. It requires a complete pre-registration object. The empirical instantiation E_C must be fixed in enough detail that a reviewer can determine, before the confirmatory data are inspected, what would count as support, what would count as falsification, and what would make the test inadmissible.
The purpose of pre-registration is not bureaucratic. It is structural. It prevents CBR from moving η_c after seeing a residual, changing L_CBR after seeing the curve, expanding nuisance after a null, narrowing nuisance after an anomaly, replacing rival models after the fact, or selecting a favorable scoring rule once the outcome is known.
A protocol-ready CBR test must therefore define the full empirical object:
E_C = ⟨π, ρ, C, 𝒜(C), ℛ_C, Θ_CBR, η, g, η_c, I_c, L_CBR, B, N, Δ_N, M_rival, V, D, S, κ, τ, χ_C⟩
before confirmatory interpretation begins.
The standard is:
If the empirical object is not fixed before interpretation, the test is not confirmatory.
16.1 Context Registration
The pre-registration must begin by specifying the physical context C.
This includes the physical system, apparatus, state space or Hilbert-space description, record-bearing structures, environmental couplings relevant to record formation, timing relations, accessibility-relevant degrees of freedom, protocol family, and primary observable V(η).
The registration must be detailed enough to support the construction of 𝒜(C). If C is too vague to determine the admissible channel class, then the test cannot proceed to adversarial exposure.
The required declaration is:
C is fixed before 𝒜(C), η, η_c, nuisance, rivals, and verdict rules are evaluated.
If C changes after data inspection in a way that affects the verdict, the empirical instantiation changes.
Thus:
post-data change of C ⇒ E′_C ≠ E_C
16.2 Admissible-Class Registration
The pre-registration must state the preliminary candidate class Ch(C) and the full filtration trace:
Ch(C) → F₁(C) → F₂(C) → F₃(C) → F₄(C) → F₅(C) → F₆(C) → 𝒜(C)
with:
𝒜(C) = F₆(C) / ≈_op
For each filtration stage, the protocol must state what is being excluded and why.
F₁ must specify dynamical compatibility.
F₂ must specify representational invariance.
F₃ must specify record-structural coherence.
F₄ must specify accessibility consistency.
F₅ must specify probabilistic non-insertion.
F₆ must specify empirical exposure eligibility.
The operational equivalence relation must also be declared. The protocol must state when two surviving channels are considered operationally equivalent and therefore members of the same admissible verdict class.
The required declaration is:
𝒜(C) is fixed by filtration before the confirmatory data are interpreted.
If 𝒜(C) is expanded, narrowed, or reinterpreted after data inspection, the result is not a rescue of the original test. It is a new empirical instantiation.
16.3 Formal Target Registration
The pre-registration must identify the formal CBR target under test:
π(E_C) ∈ 𝒜(C)
The target may be a single channel, an operational equivalence class of channels, or a declared channel-family. But it must be stated before outcome inspection.
The registration must also explain why π(E_C) survives the admissibility filtration and belongs to 𝒜(C).
The required declaration is:
The empirical test targets π(E_C), and π(E_C) belongs to 𝒜(C).
If no formal target is declared, the experiment may be a quantum optics experiment, a delayed-choice experiment, or an exploratory accessibility experiment, but it is not a valid empirical CBR test.
16.4 Operational Equivalence Registration
The pre-registration must define:
ρ(E_C) = [E_C]_op
The exposure verdict belongs to the operational equivalence class of the test, not to a preferred notation or description.
The registration must state which changes are operationally null and which changes create a new test. For example, notational relabeling, equivalent parameter naming, or equivalent mathematical presentation may be operationally null. But changing η_c, L_CBR, B, N, Δ_N, M_rival, S, κ, τ, or χ_C is verdict-bearing and therefore creates a new E′_C if performed after data inspection.
The required declaration is:
χ_C acts on [E_C]_op, not on arbitrary descriptions of E_C.
This prevents description-dependent verdicts.
16.5 Accessibility Calibration Registration
The pre-registration must define the operational accessibility parameter η and the calibration map:
η = g(s)
where s denotes controlled laboratory settings.
The registration must specify the calibration method, calibration dataset, uncertainty model, allowed transformations, and forbidden post-data adjustments.
The calibration must be independent of the residuals used to claim support or falsification.
The required declaration is:
η is fixed by accessibility evidence, not by the anomaly it later explains.
If η is inferred from the same residual used to claim CBR support, the test is inadmissible.
16.6 Critical-Regime Registration
The pre-registration must state how η_c is fixed.
Three forms are admissible.
The strongest form derives η_c from burden geometry and protocol structure:
η_c = f(Ξ_C, Ω_C, Λ_C, protocol structure)
The moderate form bounds η_c in a protocol-derived interval:
η_c ∈ [η_−, η_+]
The weak but admissible form pre-registers a finite critical window:
η_c ∈ I_pre
In all cases, the critical interval I_c and width δ must be fixed before confirmatory data inspection.
The required declaration is:
η_c, I_c, and δ are fixed before the residuals are inspected.
If η_c is moved, widened, narrowed, or reinterpreted after data in a verdict-changing way, the test is inadmissible as a confirmatory test.
16.7 Signature Registration
The predicted CBR signature L_CBR must be restricted before data.
The registration must state:
the location of the signature,
the critical interval I_c,
the width or width bound,
the sign or reason for sign symmetry,
the minimum effect size ε,
the morphology,
the relation to Λ_C,
the observable V(η),
and the detection threshold τ.
The required declaration is:
L_CBR is a prediction, not a residual label.
If the alleged signature is defined only after the data are inspected, the result cannot be CBR-supportive.
16.8 Burden-Parameter Registration
The registration must state the treatment of:
α, β, γ
These may be fixed values, theory-level constants, or predeclared bounded ranges. But they cannot be moved after data to amplify support or suppress falsification.
The γ parameter requires special attention because it governs the accessibility-consistency burden Λ_C in the empirical accessibility model. If γ is allowed to become effectively zero after a null, then the accessibility signature can be evaded. That is inadmissible unless such a possibility was declared before the test.
The required declaration is:
α, β, and γ are not post-data fit knobs.
16.9 Baseline Registration
The baseline class B must be declared before data.
The registration must state which standard quantum/decoherence behaviors are included, what baseline flexibility is allowed, what control data justify the baseline, and what localized features are excluded unless independently justified.
The required declaration is:
B is a fair comparator, not a straw null and not a post-hoc absorber.
If B is too narrow, ordinary behavior may look like CBR. If B is too broad, genuine deviation may be absorbed. The admissible baseline must avoid both failures.
16.10 Nuisance Registration
The nuisance class N and nuisance envelope Δ_N must be declared before confirmatory interpretation.
The registration must specify nuisance sources relevant to the platform, including phase drift, detector response, source stability, imperfect erasure, calibration uncertainty, sampling effects, post-selection bias, and reconstruction bias where applicable.
The nuisance envelope is:
Δ_N(η) = sup{|N(η; θ_N)| : N ∈ N}
The required declaration is:
Δ_N is externally justified before the residual is interpreted.
If Δ_N is expanded after data to dismiss a failure or narrowed after data to manufacture support, the test is inadmissible.
16.11 Rival-Model Registration
The rival library M_rival must be declared before data.
At minimum, it must include:
smooth baseline plus nuisance,
CBR accessibility model,
baseline curvature,
phase drift,
detector saturation,
imperfect erasure,
source coherence drift,
η-axis miscalibration,
generic localized anomaly,
and reconstruction bias.
The required declaration is:
CBR must defeat hostile rivals, not merely a weak null.
If the rival library omits obvious non-CBR mechanisms capable of mimicking the signature, the support claim is not adversarially closed.
16.12 Model-Selection Registration
The scoring rule S, separation margin κ, and detection threshold τ must be declared before data.
The registration must explain how model flexibility is penalized, how rival models are compared, and what margin is required for a supportive verdict.
The required declaration is:
The verdict rule is fixed before the verdict is known.
If the scoring rule is selected after observing which rule favors CBR, the test is inadmissible.
16.13 Sensitivity and Control Registration
The protocol must state the sampling density across η, the sampling density inside I_c, the power to detect ε, the positive-control recovery procedure, and the negative-control regions.
A null cannot falsify CBR if the experiment could not detect the predicted effect.
A positive anomaly cannot support CBR if the same feature appears in negative-control regions.
The required declaration is:
The test must be able to detect what it claims to test and localize what it claims to identify.
16.14 Verdict Registration
The protocol must state the three possible verdicts.
A supportive verdict requires admissibility, signature appearance inside I_c, match to L_CBR, residual magnitude beyond Δ_N + τ, negative-control specificity, and victory over all declared rivals by at least κ.
A falsifying verdict requires admissibility, sufficient sensitivity, valid nuisance bounds, adequate sampling of I_c, and persistent baseline-class behavior across the critical regime with no predicted accessibility signature beyond tolerance.
An inadmissible verdict applies if calibration, admissibility, fixity, nuisance bounds, rival declaration, sensitivity, exposure invariance, or verdict-rule fixation fails.
The required declaration is:
χ_C is fixed before interpretation.
16.15 No-Rescue Registration
Finally, the protocol must state that post-failure modification of verdict-bearing commitments defines a new empirical instantiation.
Changing any of the following after failure creates E′_C:
η_c,
I_c,
δ,
γ,
L_CBR,
B,
N,
Δ_N,
M_rival,
S,
κ,
τ,
χ_C,
π(E_C),
or 𝒜(C).
The required declaration is: A failed E_C remains failed. Revision creates E′_C.
16.16 Section Result
This section defines protocol-ready pre-registration as the complete fixation of the empirical instantiation before confirmatory interpretation.
The result is:
No complete pre-registration object, no confirmatory CBR test.
A CBR experiment may still be exploratory without this structure. But it cannot claim adversarially closed support or falsification.
17. Adversarial Exposure Trichotomy
The exposure map χ_C must assign every proposed empirical CBR instantiation to one of three verdict classes:
supportive
falsifying
inadmissible
This trichotomy is not a rhetorical convenience. It is necessary to prevent two common errors.
The first error is treating a weak or underdefined experiment as weak support.
The second error is treating a weak or underpowered null as falsification.
The trichotomy solves both problems. If the test is not empirically admissible, it is neither supportive nor falsifying. It is inadmissible. If it is admissible, then the fixed verdict rules determine whether the result supports or falsifies the tested instantiation.
17.1 The Three Verdict Classes
The first verdict class is supportive.
A supportive verdict means that the tested empirical instantiation survived adversarial exposure and produced the predicted CBR signature under predeclared conditions while defeating hostile rivals.
The second verdict class is falsifying.
A falsifying verdict means that the tested empirical instantiation made a determinate prediction, the experiment was capable of detecting that prediction, nuisance bounds held, and the predicted signature did not appear under strong-null conditions.
The third verdict class is inadmissible.
An inadmissible verdict means that the test never earned confirmatory status. It lacked some required condition of adversarial exposure: calibration, filtration, target projection, η_c fixity, signature restriction, nuisance bounds, rival library, model-selection rule, test-invariance, sensitivity, or no-rescue compliance.
These three verdicts are exhaustive for adversarial exposure.
17.2 Supportive Verdict
A supportive verdict is the strongest positive empirical status available to a CBR instantiation under this framework.
It requires that:
E_C ∈ Emp_adm(C)
π(E_C) ∈ 𝒜(C)
χ_C is invariant on [E_C]_op
η is independently calibrated
η_c and I_c are fixed before data
L_CBR is restricted before data
B, N, Δ_N, and M_rival are fixed before data
S, κ, and τ are fixed before data
and the predicted signature appears inside I_c.
The observed feature must match L_CBR in location, width, sign, magnitude, morphology, and relation to Λ_C.
It must exceed the nuisance envelope:
|V_obs(η) − V_B(η)| > Δ_N(η) + τ
It must be absent from negative-control regions.
Finally, the CBR model M₁ must defeat every declared rival by at least κ.
Only then:
χ_C([E_C]_op) = supportive
A supportive verdict does not prove CBR as final physics. It supports the tested instantiation against declared rivals under adversarially closed conditions.
17.3 Falsifying Verdict
A falsifying verdict is available only after empirical admissibility is satisfied.
The test must have had a real chance to detect the predicted effect. It must not be a weak null, an underpowered null, or a nuisance-contaminated null.
A falsifying verdict requires that:
E_C ∈ Emp_adm(C)
π(E_C) ∈ 𝒜(C)
χ_C is invariant on [E_C]_op
η is independently calibrated
η_c and I_c are fixed
L_CBR is restricted
B is validated
N and Δ_N remain valid
M_rival is declared
S, κ, and τ are fixed
the experiment has power to detect ε
I_c is adequately sampled
and only validated baseline-class behavior appears across I_c, with no strong-form or weak-form CBR accessibility signature beyond the declared tolerance.
Only then:
χ_C([E_C]_op) = falsifying
This verdict falsifies the tested empirical instantiation E_C. It may contribute to canonical-model failure if reproduced across the declared protocol family under detectability-valid conditions.
17.4 Inadmissible Verdict
The inadmissible verdict applies whenever the test fails to satisfy adversarial exposure conditions.
A test is inadmissible if:
C is under-specified,
𝒜(C) lacks a filtration trace,
π(E_C) ∉ 𝒜(C),
η is not independently calibrated,
η_c is moved after data,
L_CBR is unrestricted,
α, β, or γ are moved after data,
B, N, or Δ_N are post-hoc,
M_rival is missing or post-hoc,
S, κ, or τ is selected after data,
χ_C is not invariant under ≈_op,
the test lacks power to detect ε,
the alleged signature is absorbed by nuisance,
the alleged signature is absorbed by a rival model,
or a failed instantiation is retroactively revised and treated as surviving.
An inadmissible result is not weak support.
It is not weak falsification.
It is failure to enter the exposure relation.
Thus:
χ_C([E_C]_op) = inadmissible
17.5 Theorem 8: Adversarial Exposure Trichotomy
For every proposed empirical CBR instantiation E_C, an adversarially closed exposure framework assigns exactly one verdict to [E_C]_op:
supportive
falsifying
or:
inadmissible
provided χ_C is well-defined.
17.6 Proof
If E_C fails empirical admissibility, then by definition it cannot be supportive or falsifying. The verdict is inadmissible.
If E_C satisfies empirical admissibility, then χ_C is defined on [E_C]_op under predeclared rules. The support path and strong-null path are disjoint. The support path requires the predicted signature to appear in I_c, exceed nuisance, match L_CBR, and defeat rivals. The strong-null path requires the predicted signature not to appear under conditions sufficient to detect it.
If the support conditions are satisfied, the verdict is supportive. If the strong-null conditions are satisfied, the verdict is falsifying. If neither path can be completed because some exposure condition fails, the verdict is inadmissible.
Therefore the trichotomy is exhaustive under a well-defined χ_C.
17.7 Corollary: Inadmissibility Is a Verdict, Not a Gap
The inadmissible classification is not an absence of judgment. It is a judgment about the test’s failure to satisfy exposure conditions.
This matters because it prevents weak experiments from being rhetorically inflated.
A poorly calibrated anomaly is not partial support.
A weak null is not partial falsification.
Both are inadmissible as confirmatory tests.
17.8 Corollary: Support and Falsification Are Both Hard
Under adversarial closure, CBR cannot obtain easy support from a residual, and critics cannot obtain easy falsification from a weak null.
Both positive and negative verdicts require admissibility.
This symmetry is essential. Adversarial exposure is not designed to protect CBR. It is designed to make any verdict fair, fixed, and reviewable.
17.9 Section Result
This section establishes that every adversarially closed CBR test must end in one of three statuses:
supportive
falsifying
inadmissible
The trichotomy gives the exposure map operational completeness.
No result may float between categories by rhetorical interpretation.
The verdict must follow from χ_C.
18. What This Paper Proves and Does Not Prove
A theory-hardening paper must be precise about its claim. If it claims too little, it fails to strengthen the program. If it claims too much, it becomes vulnerable to easy dismissal.
This paper claims a strong but scoped result:
It defines the adversarial closure standard under which empirical CBR claims become valid, invalid, supportive, falsifying, or inadmissible without target movement, anomaly absorption, description dependence, or post-failure rescue.
It does not claim that CBR is experimentally confirmed. It does not claim that all possible realization-law alternatives are false. It does not claim final universal closure of quantum foundations.
Its contribution is different: it makes empirical CBR maximally reviewable.
18.1 What This Paper Proves
First, the paper proves that the admissible class 𝒜(C) can be made constructive rather than merely named.
The construction is:
𝒜(C) = F₆(C) / ≈_op
with the filtration excluding dynamical leakage, representational dependence, record incoherence, accessibility arbitrariness, probability insertion, and empirical idleness.
Second, the paper proves the Minimal Filtration Theorem. Each filtration stage is necessary because each blocks a distinct hostile-review failure mode. Removing any stage reopens arbitrariness.
Third, the paper proves that empirical instantiations and formal channels are different types of objects. The correct relation is:
π(E_C) ∈ 𝒜(C)
not:
E_C ∈ 𝒜(C)
Fourth, the paper proves that ℛ_C is burden-forced within the adversarial CBR theorem class. The canonical burden:
ℛ_C = αΞ_C + βΩ_C + γΛ_C
is not merely a convenient functional if one accepts the stated admissibility constraints. It is the burden representation of representational, record-structural, and accessibility admissibility.
Fifth, the paper proves that an empirical exposure map is required:
χ_C : Emp_adm(C) / ≈_op → {supportive, falsifying, inadmissible}
Without χ_C, an experiment does not give CBR a determinate empirical verdict.
Sixth, the paper proves exposure invariance. Operationally equivalent empirical descriptions must yield the same verdict:
E_C ≈_op E′_C ⇒ χ_C(E_C) = χ_C(E′_C)
Seventh, the paper proves critical-regime fixity. η_c must be derived, bounded, or pre-registered before data. Post-data movement of η_c makes the test inadmissible.
Eighth, the paper proves anomaly-absorption closure. A residual is not CBR-supportive if hostile non-CBR rivals can absorb it within τ.
Ninth, the paper proves no-rescue falsification. A failed admissible E_C cannot be rescued by post-data modification. Such modification defines a new E′_C.
Tenth, the paper proves the adversarial exposure trichotomy. Every well-formed exposure attempt is supportive, falsifying, or inadmissible.
Together these results define the adversarial closure standard for empirical CBR.
18.2 What This Paper Does Not Prove
This paper does not prove that CBR is true.
It does not prove that CBR has been experimentally confirmed.
It does not prove that the accessibility signature will appear in nature.
It does not prove that every possible realization-law alternative is false.
It does not prove universal Born-rule closure across every possible admissibility geometry.
It does not prove that η_c is already exactly derivable in every physical protocol.
It does not prove that every implementation of the designated protocol family will have sufficient sensitivity.
It does not prove that all nuisance effects can be eliminated.
It does not prove that future CBR revisions are impossible.
It does not prove that a supportive result would establish CBR as final physics.
These non-claims are not weaknesses. They are boundaries. They keep the paper’s result exact.
18.3 What the Paper Changes
The paper changes the status of empirical CBR in a specific way.
Before adversarial closure, a critic could object that CBR might still move η_c, redefine accessibility, absorb anomalies, adjust nuisance, omit rivals, or revise after failure.
After adversarial closure, those moves are no longer available to a valid empirical claim.
CBR can still be tested.
CBR can still be supported.
CBR can still be falsified.
CBR can still be revised.
But every one of those actions must occur under fixed rules.
The paper therefore changes CBR from:
a theory with an empirical signature
to:
a theory with a complete adversarial verdict standard
That is the strengthening.
18.4 What a Successful Use of This Paper Would Look Like
A successful application of this paper would not merely cite the adversarial closure standard. It would instantiate it.
A protocol-ready CBR test would specify C, construct 𝒜(C), identify π(E_C), calibrate η independently, derive or pre-register η_c, restrict L_CBR, declare B, N, Δ_N, M_rival, S, κ, and τ, audit positive and negative controls, and define χ_C before confirmatory data inspection.
Then the result would be classified without reinterpretation.
If the predicted signature appeared, exceeded nuisance, matched L_CBR, and defeated rivals, the result would be supportive.
If the predicted signature failed to appear under strong-null conditions, the result would be falsifying.
If the test lacked calibration, sensitivity, invariance, rival separation, or fixed verdict rules, the result would be inadmissible.
That is what adversarial exposure closure demands.
18.5 What a Failed Use of This Paper Would Look Like
A failed application would use the vocabulary of adversarial closure without accepting its constraints.
Examples include:
claiming support from a residual without independent η calibration,
moving η_c after seeing the residual,
changing L_CBR after data,
declaring nuisance only after the outcome,
omitting obvious rival models,
choosing the scoring rule post-hoc,
treating operationally equivalent descriptions differently,
or revising a failed E_C while claiming the original survived.
Such uses would not strengthen CBR. They would violate the paper.
The adversarial closure standard must be enforced, not merely named.
18.6 Section Result
This section fixes the scope of the paper.
The paper proves a standard, not an experimental result.
It proves adversarial closure conditions, not CBR truth.
It makes CBR harder to support cheaply and harder to falsify unfairly.
Its central achievement is that it makes empirical CBR claims reviewable under exact verdict rules.
The result is:
CBR cannot move the target, absorb anomalies, depend on description choices, or revise away failure while still claiming adversarially closed empirical status.
19. Why This Makes CBR Harder to Dismiss
A theory candidate becomes easier to dismiss when its central objects remain flexible. If the admissible class can move, the theory can be accused of selecting its domain after the fact. If the critical regime can move, the theory can be accused of chasing anomalies. If nuisance bounds can expand or contract after data, the theory can be accused of protecting itself selectively. If rival models are omitted, the theory can be accused of mistaking a generic artifact for a theory-specific signal. If failed tests can be revised retroactively, the theory can be accused of being unfalsifiable in practice.
The adversarial closure standard is designed to remove those objections.
It does not make CBR true. It makes the empirical standing of CBR harder to attack because every major point of flexibility is converted into a fixed, auditable commitment.
19.1 The Vagueness Objection
A critic may object:
𝒜(C) is vague.
The adversarial closure response is that 𝒜(C) is not merely named. It is constructed:
𝒜(C) = F₆(C) / ≈_op
The filtration must show how candidate channels pass through dynamical compatibility, representational invariance, record-structural coherence, accessibility consistency, probabilistic non-insertion, and empirical exposure eligibility.
This changes the burden of criticism. A critic can no longer object only that “the admissible class is unclear.” The critic must identify which filtration stage is invalid, incomplete, redundant, or incorrectly applied.
That is progress. It turns a global vagueness objection into a local technical dispute.
19.2 The Convenience Objection
A critic may object:
ℛ_C = αΞ_C + βΩ_C + γΛ_C is chosen because it is convenient.
The adversarial closure response is the Burden Representation Theorem. Within the stated theorem class, the burden coordinates are forced by the admissibility requirements.
Representational invariance forces an Ξ-type burden.
Record-structural coherence forces an Ω-type burden.
Accessibility consistency forces a Λ-type burden.
Probabilistic non-insertion blocks a separate probability-fitting term.
Empirical exposure blocks idle terms that have no operational consequence.
Therefore, within the adversarial CBR class, the burden functional is not a decorative choice. It is the scalar representation of the surviving admissibility burdens.
A critic may still reject the theorem’s assumptions. But then the debate becomes precise: which admissibility burden is unnecessary, or which representation condition fails?
19.3 The Target-Movement Objection
A critic may object:
η_c can be moved to wherever the anomaly appears.
The adversarial closure response is the Critical-Regime Fixity Theorem.
η_c must be derived, bounded, or pre-registered before data. The critical interval I_c and width δ must also be fixed before confirmatory interpretation. Post-data movement of η_c, widening of I_c, narrowing of I_c, or reinterpretation of the critical regime invalidates the confirmatory test.
This blocks one of the most serious empirical objections. The theory cannot search for a residual and then declare that location to be the critical accessibility regime.
The target must be fixed before the shot is fired.
19.4 The Anomaly-Absorption Objection
A critic may object:
Any anomaly can be called the CBR signature.
The adversarial closure response is the Anomaly-Absorption Theorem.
A residual is not CBR-supportive merely because it is unexpected, localized, or near η_c. It must match the predeclared L_CBR, exceed the nuisance envelope, and resist absorption by hostile non-CBR rivals.
The support path is:
exceed nuisance → match L_CBR → defeat rivals
Skipping any step destroys CBR-specific support.
Thus the theory cannot claim an anomaly merely because the anomaly is interesting. The anomaly must be the predicted, bounded, rival-resistant accessibility signature.
19.5 The Nuisance Objection
A critic may object:
The effect could be apparatus noise, detector behavior, source drift, imperfect erasure, or reconstruction bias.
The adversarial closure response is that nuisance must be fixed as an external audit object.
The nuisance class N and nuisance envelope Δ_N must be declared before data and justified by independent apparatus characterization. A residual inside Δ_N + τ cannot support CBR. A null under uncontrolled nuisance cannot falsify CBR.
This symmetry is important. Nuisance control protects CBR from false support and false falsification.
The rule is:
No bounded nuisance, no verdict.
19.6 The Rival-Model Objection
A critic may object:
CBR only beat a weak null, not serious alternatives.
The adversarial closure response is the hostile rival library.
CBR must defeat models involving baseline curvature, phase drift, detector saturation, imperfect erasure, source coherence drift, η-axis miscalibration, generic localized anomaly, reconstruction bias, and any additional platform-specific rivals.
The CBR model M₁ is not privileged by default. It must win against M_rival under a predeclared scoring rule.
This blocks the common failure mode in which a theory claims support because it fits better than an oversimplified baseline while ignoring more plausible non-CBR explanations.
19.7 The Description-Dependence Objection
A critic may object:
The result depends on how the experiment is described.
The adversarial closure response is exposure invariance.
If:
E_C ≈_op E′_C
then:
χ_C(E_C) = χ_C(E′_C)
A change in notation, parameter naming, basis representation, or equivalent model description cannot change the verdict. If the verdict changes, then either the descriptions were not operationally equivalent or the exposure map was invalid.
This makes empirical CBR internally consistent with the representational-invariance burden already present in canonical CBR.
The empirical verdict must be invariant under irrelevant redescription, just as the realization law must be invariant under irrelevant representation.
19.8 The Revision Objection
A critic may object:
CBR can always revise after failure.
The adversarial closure response is the No-Rescue Theorem.
Revision is allowed. Retroactive rescue is not.
If an empirically admissible E_C fails under its own strong-null condition, then changing η_c, γ, L_CBR, B, N, Δ_N, M_rival, S, κ, τ, χ_C, π(E_C), or 𝒜(C) defines a new E′_C.
The failed E_C remains failed.
This distinction is crucial. It allows scientific development while preserving falsification.
CBR may evolve, but a failed instantiation cannot be rewritten as having survived.
19.9 The Weak-Falsification Objection
A critic may object:
A null result should falsify CBR.
The adversarial closure response is scoped falsification.
A null falsifies the tested instantiation only if the experiment was empirically admissible, calibrated, sensitive, nuisance-bounded, rival-aware, and sampled across the critical regime. A weak null is not a falsification.
This is not special pleading. It is the same standard applied to any theory with a bounded predicted signal: the experiment must have been capable of detecting what it claims not to have seen.
The result is a fair symmetry:
cheap anomalies do not support CBR, and weak nulls do not falsify CBR.
Only adversarially admissible tests produce verdicts.
19.10 Section Result
This paper makes CBR harder to dismiss because it removes the easiest objections.
CBR can no longer be dismissed as having a vague admissible class, because 𝒜(C) is constructed by filtration.
It can no longer be dismissed as having a convenient burden functional, because ℛ_C is represented as forced by the admissibility burdens.
It can no longer be dismissed as chasing anomalies, because η_c must be fixed before data.
It can no longer be dismissed as absorbing residuals, because support requires hostile rival defeat.
It can no longer be dismissed as description-dependent, because χ_C must be invariant over operational equivalence classes.
It can no longer be dismissed as unfalsifiable by revision, because the no-rescue rule prevents retroactive survival.
The result is not that CBR is proven.
The result is that CBR becomes reviewable under exact adversarial rules.
20. Relationship to the Canonical Closure Paper
This paper does not replace the canonical closure paper. It depends on it.
The canonical closure paper states CBR as a candidate realization law. It defines the canonical law form, restricts the admissible class, establishes restricted uniqueness up to operational equivalence, proves local probability closure within canonical admissibility, introduces η and η_c, identifies a designated delayed-choice record-accessibility protocol family, imposes nuisance separation, and states a strong-null failure condition. Its theorem spine consists of Restricted Canonical Uniqueness, the Accessibility-Signature Theorem, and the Failure Criterion.
The present paper takes that canonical object and asks how it must be empirically exposed.
The relationship is therefore:
The canonical closure paper fixes the theory object.
This paper fixes the adversarial testing object.
The canonical paper says:
Here is CBR as a canonically specified and experimentally vulnerable theory candidate.
This paper says:
Here is the closure standard under which no empirical CBR claim can move the target, absorb anomalies, depend on description choices, or rescue failure after the fact.
20.1 The Formal Side: Realization Selection
The canonical theory gives the realization-selection structure:
Φ*_C = argmin{ℛ_C(Φ) : Φ ∈ 𝒜(C)}
with:
ℛ_C(Φ) = αΞ_C(Φ) + βΩ_C(Φ) + γΛ_C(Φ)
This is the formal side of CBR.
It answers:
What channel, or operational channel class, is selected as the realized outcome structure in context C?
The canonical paper’s primary burden is to show that this law form is not arbitrary within its declared admissibility structure, and that it is sufficiently fixed to incur empirical risk.
20.2 The Empirical Side: Exposure Classification
The present paper gives the exposure-classification structure:
χ_C : Emp_adm(C) / ≈_op → {supportive, falsifying, inadmissible}
with:
π(E_C) ∈ 𝒜(C)
and:
ρ(E_C) = [E_C]_op
This is the empirical side of CBR.
It answers:
What verdict does a proposed empirical instantiation receive under fixed adversarial rules?
The burden here is not to restate the realization law. The burden is to prevent empirical interpretation from becoming plastic after the fact.
20.3 Why Both Papers Are Needed
The canonical closure paper without adversarial exposure would define a serious theory object, but reviewers could still ask whether the empirical test can move η_c, redefine η, omit rivals, absorb nuisance, or revise after failure.
The adversarial exposure paper without canonical closure would define strict test rules, but without a canonical theory object to test.
The two are complementary.
Canonical closure provides:
the law form,
the admissible class,
the burden functional,
restricted uniqueness,
local weighting closure,
η,
η_c,
the accessibility signature,
and the strong-null failure condition.
Adversarial exposure closure provides:
constructive 𝒜(C),
typed projection π(E_C),
operational exposure class [E_C]_op,
invariant verdict map χ_C,
critical-regime fixity,
hostile rival separation,
external audit requirements,
pre-registration standards,
scoped failure,
and no-rescue falsification.
Together, they turn CBR into a theory program with both a formal law object and an adversarial empirical verdict standard.
20.4 How This Paper Strengthens the Canonical Failure Criterion
The canonical closure paper already states a failure criterion: if the designated protocol family shows only baseline-class behavior across the accessibility-critical regime under detectability-valid conditions, then the instantiated canonical model is false.
The present paper strengthens that condition by specifying the adversarial machinery required for such a verdict to be valid.
It asks:
Was η independently calibrated?
Was η_c fixed?
Was I_c predeclared?
Was L_CBR restricted?
Was nuisance bounded?
Were rivals declared?
Was the model-selection rule fixed?
Was the experiment sensitive enough?
Was the verdict invariant under equivalent descriptions?
Was post-failure rescue forbidden?
Only when those conditions are satisfied does the failure criterion become an adversarially closed falsification.
Thus the present paper does not weaken the canonical failure condition. It sharpens it.
20.5 How This Paper Strengthens the Accessibility-Signature Claim
The canonical closure paper states that if accessibility enters the realization law nontrivially through Λ_C, the response cannot remain globally contained in the declared smooth baseline class across the full admissible η-domain. Under stronger regularity assumptions, the response is localized near η_c as a derivative break or kink; under weaker assumptions, a bounded non-baseline deviation persists in a neighborhood of η_c.
The present paper adds the conditions under which such a signature can be claimed empirically.
It requires that the signature:
be predeclared,
be tied to Λ_C,
appear inside the fixed critical interval,
exceed Δ_N + τ,
be absent from negative controls,
and defeat hostile rivals.
This prevents a generic anomaly from being rebranded as the accessibility signature.
Thus the present paper converts the accessibility-signature theorem into an adversarial empirical standard.
20.6 How This Paper Strengthens Restricted Uniqueness
The canonical closure paper claims restricted uniqueness up to operational equivalence within the admissible class.
The present paper extends that operational-equivalence discipline to empirical verdicts.
On the formal side:
Φ ∼_op Ψ ⇒ same realization verdict class
On the empirical side:
E_C ≈_op E′_C ⇒ χ_C(E_C) = χ_C(E′_C)
This is a deep structural parallel.
CBR does not merely say that formal realization selection must be invariant under operational equivalence. It now also says empirical verdicts must be invariant under operational equivalence.
That makes the empirical framework internally CBR-like rather than merely methodological.
20.7 Section Result
The canonical closure paper and this adversarial closure paper form a two-part structure.
The canonical paper supplies:
the realization-selection object.
The present paper supplies:
the exposure-classification object.
The combined structure is:
Φ*_C = argmin{ℛ_C(Φ) : Φ ∈ 𝒜(C)}
and:
χ_C : Emp_adm(C) / ≈_op → {supportive, falsifying, inadmissible}
The first prevents arbitrary realization selection.
The second prevents arbitrary empirical interpretation.
Together they define CBR as both a canonically specified and adversarially exposed realization-law candidate.
21. Final Conclusion
CBR is strongest not when it can explain anomalies.
CBR is strongest when it forbids itself from explaining anomalies it did not lawfully predict.
That is the central meaning of adversarial exposure closure.
The canonical CBR paper already gives the program a formal spine: a context C, a restricted admissible class 𝒜(C), a burden functional ℛ_C, a selected channel Φ*_C, restricted uniqueness up to operational equivalence, local probability closure, accessibility parameter η, critical regime η_c, designated protocol family, nuisance separation, detectability conditions, and a strong-null failure criterion.
The present paper adds the adversarial spine.
It says that before CBR can claim empirical support or suffer empirical falsification, the following must be fixed:
the admissibility filtration,
the admissible class 𝒜(C),
the formal target π(E_C),
the operational exposure class [E_C]_op,
the exposure map χ_C,
the accessibility calibration η = g(s),
the critical regime η_c or I_c,
the predicted signature L_CBR,
the baseline class B,
the nuisance class N,
the nuisance envelope Δ_N,
the hostile rival library M_rival,
the scoring rule S,
the separation margin κ,
the detection threshold τ,
the strong-null condition,
and the no-rescue rule.
A theory that fixes all of these before interpretation is not hiding from empirical risk.
It is entering empirical risk under adversarial conditions.
21.1 The Closure Standard
The final adversarial closure standard is:
𝒜(C) = F₆(C) / ≈_op
π(E_C) ∈ 𝒜(C)
ρ(E_C) = [E_C]_op
χ_C : Emp_adm(C) / ≈_op → {supportive, falsifying, inadmissible}
E_C ≈_op E′_C ⇒ χ_C(E_C) = χ_C(E′_C)
strong-null failure of E_C cannot be rescued by post-data modification
These expressions summarize the paper.
The admissible class is constructed, not chosen.
The empirical target is projected, not assumed.
The exposure object is operational, not descriptive.
The verdict map is invariant, not presentation-dependent.
Failure is scoped, not evasive.
Revision is allowed, but not retroactive.
21.2 What CBR Gains
Under this standard, CBR gains five forms of strength.
First, it gains domain discipline. 𝒜(C) is no longer a vague admissible class. It is the result of an auditable filtration.
Second, it gains burden discipline. ℛ_C is not treated as a convenient fit function. It is the burden representation of the admissibility structure.
Third, it gains empirical discipline. η, η_c, L_CBR, B, N, M_rival, S, κ, and τ must be fixed before confirmatory interpretation.
Fourth, it gains invariance discipline. Equivalent descriptions of the same test must receive the same verdict.
Fifth, it gains failure discipline. A failed instantiation remains failed; post-failure revision defines a new test.
These are not cosmetic improvements. They are the conditions under which CBR can be taken seriously by hostile review.
21.3 What CBR Gives Up
Adversarial closure also forces CBR to give things up.
It gives up the ability to call any anomaly a signature.
It gives up the ability to move η_c after data.
It gives up the ability to redefine η after seeing residuals.
It gives up the ability to expand nuisance selectively.
It gives up the ability to ignore rival artifacts.
It gives up the ability to change scoring rules after the outcome.
It gives up the ability to treat equivalent descriptions differently.
It gives up the ability to revise a failed instantiation and pretend it survived.
These losses are strengths.
A theory candidate becomes more credible when it forbids itself from using easy escape routes.
21.4 The Final Scientific Posture
This paper does not claim that CBR is experimentally confirmed.
It does not claim that CBR has defeated all rival theories.
It does not claim that the accessibility signature must appear in ordinary measurement settings.
It does not claim that every possible realization-law alternative has been eliminated.
Its claim is narrower and stronger:
If CBR is to make an empirical claim, that claim must be adversarially closed.
That means the claim must be generated by a fixed admissibility filtration, classified by an invariant exposure map, tested against hostile rivals, audited externally, and protected from post-failure rescue.
This is the posture of a serious candidate theory.
Not certainty.
Not confirmation.
Not finality.
But disciplined exposure.
21.5 Final Statement
The canonical CBR sequence makes outcome realization a constrained law-selection problem.
This paper makes empirical CBR a constrained verdict-classification problem.
The formal theory asks:
Which realization channel is selected?
The adversarial empirical theory asks:
Which verdict is forced by the fixed test?
The final answer is:
supportive
falsifying
or:
inadmissible
Nothing else counts as a confirmatory verdict.
That is the closure achieved here.
CBR cannot move the target.
CBR cannot absorb anomalies.
CBR cannot depend on description choices.
CBR cannot revise away failure.
CBR can still be supported.
CBR can still be falsified.
CBR can still be revised.
But only under fixed, auditable, invariant, adversarial rules.
That is what it means to move from canonical CBR to adversarial exposure closure.
Appendix A: Adversarial Decision Sequence
The decision sequence is the operational form of χ_C. It must be applied in order. Failure at an admissibility stage prevents the test from reaching support or falsification.
The first question is whether the physical context C is specified. The context must include the system, apparatus, record-bearing structures, accessibility-relevant degrees of freedom, protocol family, timing relations, and primary observable. If C is not specified, the test is inadmissible.
The second question is whether 𝒜(C) has been constructed by the filtration from Ch(C) through F₁, F₂, F₃, F₄, F₅, and F₆, followed by quotienting under operational equivalence. If the filtration trace is missing, the test is inadmissible.
The third question is whether the empirical instantiation has a formal target π(E_C) and whether π(E_C) ∈ 𝒜(C). If not, the test is inadmissible.
The fourth question is whether η is independently calibrated. If η is inferred from the same residual used to claim CBR support, the test is inadmissible.
The fifth question is whether η_c or I_c is derived, bounded, or pre-registered before data inspection. If the critical regime is moved after seeing the result, the test is inadmissible.
The sixth question is whether L_CBR is restricted before data in location, width, sign, magnitude, morphology, and relation to Λ_C. If not, the test is inadmissible.
The seventh question is whether α, β, and γ are fixed before data, or varied only within predeclared ranges. If any burden coefficient is moved after the result is known, the test is inadmissible.
The eighth question is whether B, N, and Δ_N are fixed before data. If the baseline or nuisance envelope is altered after outcome inspection, the test is inadmissible.
The ninth question is whether M_rival is declared before data and includes credible non-CBR mechanisms capable of mimicking the alleged signature. If not, the test is inadmissible.
The tenth question is whether S, κ, and τ are fixed before data. If the scoring rule, separation margin, or detection threshold is chosen after the result is known, the test is inadmissible.
The eleventh question is whether χ_C is invariant under operational equivalence. If equivalent descriptions yield different verdicts, the test is inadmissible.
The twelfth question is whether the experiment has sufficient power to detect ε inside I_c. If not, the test is inadmissible as a confirmatory test.
Only after these gates are passed can the support path or strong-null path be entered.
The support path begins by asking whether L_CBR appears inside I_c and exceeds Δ_N + τ. If not, the test enters the strong-null path. If yes, the feature must match the predeclared signature and defeat every declared rival by at least κ. If it does, the verdict is supportive. If it does not, the result is not CBR-supportive.
The strong-null path begins when L_CBR does not appear. The absence of the signature is falsifying only if η was independently calibrated, η_c was fixed, I_c was adequately sampled, B was validated, Δ_N remained valid, the experiment had sufficient power, and only baseline-class behavior appeared across I_c. If those conditions hold, the verdict is falsifying. If not, the result is inadmissible or exploratory.
If the verdict is falsifying, the no-rescue rule applies. Any later change to η_c, I_c, γ, L_CBR, B, N, Δ_N, M_rival, S, κ, τ, χ_C, π(E_C), or 𝒜(C) defines a new E′_C. It does not rescue the failed E_C.
Appendix B: External Audit Standard
Adversarial exposure requires independent audit. A CBR test cannot claim confirmatory status merely because its authors state that the relevant objects were fixed. The fixation must be inspectable.
The η calibration audit asks whether η was fixed from accessibility evidence rather than from the anomaly it later explains. Auditors must inspect the calibration protocol, calibration dataset, uncertainty model, η = g(s), allowed transformations, and forbidden post-data adjustments.
The η_c audit asks whether the critical regime was fixed before the result was known. Auditors must inspect the derivation, bounded interval, or pre-registration record for η_c, I_c, and δ. Any verdict-changing post-data movement invalidates confirmatory status.
The admissibility-filtration audit asks whether 𝒜(C) can be reconstructed from Ch(C) through F₁–F₆ and quotienting by operational equivalence. If the filtration cannot be reconstructed without knowing the outcome, the test is inadmissible.
The baseline audit asks whether B was a fair comparator. It must be broad enough to represent legitimate standard quantum/decoherence behavior but not so broad that it absorbs arbitrary anomalies.
The nuisance audit asks whether N and Δ_N were fixed before interpretation and justified by independent apparatus characterization. Auditors must inspect phase drift, detector response, source coherence, erasure imperfections, calibration uncertainty, finite sampling, post-selection, and reconstruction-bias estimates where relevant.
The rival-library audit asks whether M_rival included credible non-CBR mechanisms capable of mimicking the signature. The library must include baseline curvature, phase drift, detector saturation, imperfect erasure, source drift, η-axis miscalibration, generic localized anomaly, and reconstruction bias unless a platform-specific reason excludes one.
The model-selection audit asks whether S, κ, and τ were fixed before outcome inspection. The score must penalize flexibility and compare CBR fairly against rivals.
The blinding or held-out confirmation audit asks whether exploratory fitting was separated from confirmatory verdict assignment. Acceptable safeguards include blinding, training-confirmation splits, held-out datasets, independent replication, or pre-registered analysis pipelines.
The positive-control audit asks whether the experiment could recover an injected or synthetic effect of size ε inside I_c. If not, a null cannot falsify the prediction.
The negative-control audit asks whether the alleged signature appears outside the predicted critical regime. If the same feature appears broadly or in control regions, the result is not CBR-specific.
The no-rescue audit asks whether a failed E_C was revised honestly as a new E′_C or retroactively protected as though it had survived. Retroactive rescue violates adversarial closure.
The audit standard can be summarized in one rule:
If an external reviewer cannot reconstruct the fixed empirical object before knowing the outcome, the test is not adversarially closed.
Appendix C: CBR Kill Conditions
A CBR empirical test can terminate in three ways: inadmissibility, falsification, or support. The conditions must be stated plainly.
A test is inadmissible when it never earns confirmatory status. This occurs if C is under-specified, if 𝒜(C) lacks a filtration trace, if π(E_C) ∉ 𝒜(C), if η is not independently calibrated, if η_c is moved after data, if L_CBR is unrestricted, if α, β, or γ are changed after data, if B, N, or Δ_N are post-hoc, if M_rival is missing or post-hoc, if S, κ, or τ is selected after data, if χ_C is not invariant under operational equivalence, if the test lacks power to detect ε, if the alleged signature is absorbed by nuisance, if the alleged signature is absorbed by a rival model, or if a failed instantiation is retroactively revised and treated as surviving.
An inadmissible test does not support CBR.
It does not falsify CBR.
It fails to enter the exposure relation.
A test is falsifying when it is first empirically admissible and then satisfies the strong-null condition. This requires independent η calibration, fixed η_c and I_c, restricted L_CBR, validated B, bounded N and Δ_N, declared rivals, fixed S, κ, and τ, sufficient sensitivity, adequate sampling of I_c, and persistent baseline-class behavior across the critical regime with no predicted accessibility signature beyond tolerance.
A falsifying result defeats the tested E_C.
If repeated across the declared protocol family under detectability-valid conditions, it may defeat the present canonical accessibility model.
It does not automatically eliminate every possible future CBR revision.
A test is supportive when it is empirically admissible and the predicted L_CBR appears inside I_c, matches the predeclared form, exceeds Δ_N + τ, remains absent from negative-control regions, and defeats every declared rival by at least κ.
A supportive result supports the tested instantiation.
It does not prove CBR as final physics.
The kill condition for a failed instantiation is simple:
If E_C fails under its own fixed strong-null condition, E_C remains failed.
Any post-failure modification creates E′_C.
That is the no-rescue rule.